A recent blog article shows how to easily deploy a Polycom SIP Phone running UCS 4.1.0 firmware in a Lync environment, but in the event that the device is unable to successfully sign in to the Lync server then this is typically a TLS communications problem most often attributed to a certificate trust failure.
Lync Registration Failure
If registration of the device fails to the Lync Server the first thing to check is the device logs which are accessible through the phone’s built-in web management interface.
Check Device Logs
- Open the web management interface by simply connecting to the IP address of the phone from in a web browser, provide the Admin password (default value is ‘456’) and browse to the Diagnostics > View & Download Logs menu.
000928.720|cfg |4|00|Prov|Unknown suboption received for DHCP option 43
000928.720|cfg |4|00|Prov|Invalid STS-URI: ‘http:///anon’
000930.280|sip |4|00|doDnsListLookup(tls): doDnsSrvLookupForARecordList ‘sipinternal.mslync.net’ found no records.
000930.281|sip |4|00|doDnsListLookup(tcp): doDnsSrvLookupForARecordList ‘sipinternal.mslync.net’ found no records.
000930.281|sip |4|00|doDnsListLookup(tls): doDnsSrvLookupForARecordList ‘sipexternal.mslync.net’ found no records.
000930.281|sip |4|00|doDnsListLookup(tcp): doDnsSrvLookupForARecordList ‘sipexternal.polycomcsna.com’ found no records.
000930.456|sip |4|00|Server certificate verification failed, Untrusted Certificate
000930.456|sip |4|00|Server certificate verification failed, Untrusted Certificate
000930.457|sip |4|00|MakeTlsConnection: SSL_connect error 1
000930.457|sip |4|00|MakeTlsConnection: connection failed error -1
The log excerpt above shows what happens when the device is unable to locate the Lync Server certificate provisioning service due to missing or incorrectly configured DHCP Option 43 values.
Check Certificate Store
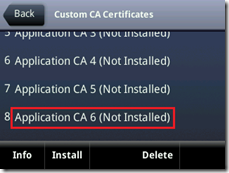
- To validate that the root certificate was not successfully downloaded press the physical Home button and then tap the following menu items: Settings > Advanced > Administration Settings > TLS Security > Custom CA Certificates and then scroll down to the bottom of the list to the Application CA 6 container.
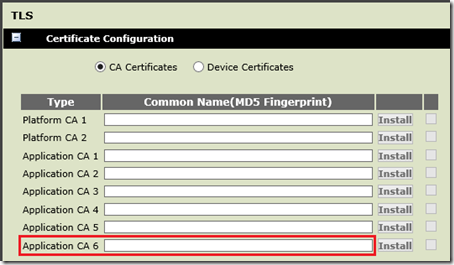
- To perform the same check using the web management interface instead browse to the Settings > Network > TLS menu and check that the Application CA 6 container is blank.
Import Root Certificate
In this scenario the device was not able to automatically download a root certificate and thus cannot establish a secure TLS connection to the Lync Server to begin the registration process.
In the event that this prerequisite configuration is not available or the phone is unable to successfully import the root certificate chain then the certificate(s) must be provided to the phone manually. Understand that the automatic download process simply uses the last Application CA 6 container as it is the least commonly used container and should prevent conflicts when multiple cert chains are loaded into the device at one time. When importing certificates manually any of the available Application CA containers can be used; the examples below will utilize Application CA 1.
There are two different processes available for manually providing a root certificate or chain of certificates to the device, either by importing an XML configuration file which contains the certificate hash(es) or by hosting a certificate file on a web server and simply pointing the device to the URL to import it.
XML Method
The approach is basically the same process as documented for the previous 4.0 release by using an XML configuration file, but the file will only contain the few parameters specific to the certificate and not all of the other parameters that used to be required for the older version.
- Follow the steps at the beginning of this article under the Preparation section entitled “Retrieving the CA Certificate Hash” to export the root certificate hash.
- Create a new XML file as instructed in the previous article, but instead only include the following two parameters: “sec.TLS.customCaCert.1” and “sec.TLS.profileSelection.SIP”.. Save the file (e.g. cert.cfg).
<?xml version=”1.0″ encoding=”utf-8″?>
<!–UCS 4.1 Lync Certificate Import File–>
<lync>
<cert sec.TLS.customCaCert.1=”” sec.TLS.profileSelection.SIP=”ApplicationProfile1″ />
</lync>
If a different container is desired simply update the last digit in the sec.TLS.customCaCert.1 parameter to a value of 1 through 6 to coincide with one of the six Application CA containers. In addition change the digit in the ApplicationProfile1 value for the second parameter to match. For example, to store a certificate in container 3 update the configuration as shown below. This approach may be needed to import a chain of multiple certificates in some environments.
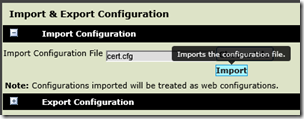
- Using the web management interface browse to the Utilities > Import & Export Configuration menu and expand Import Configuration.
- Click Choose File and then locate the XML configuration file created in the previous step (e.g. cert.cfg) and then select Import.
- If performed correctly, and the user credentials are still stored in the phone then the device should automatically register to Lync within a matters of a few seconds.
Web Server Method
There is also an alternative approach to importing the certificates on the phone that doesn’t require using these XML configuration files as shown above. Instead the certificate hash file(s) would be placed on a standard web server that the phone can connect to and then the certificate can be imported manually from the web management interface using a URL. This process is simpler than dealing with the XML configuration file and provide a single distribution point for importing the certificate.
- Follow the steps at the beginning of this article under the Preparation section entitled “Retrieving the CA Certificate Hash” to export the root certificate hash.
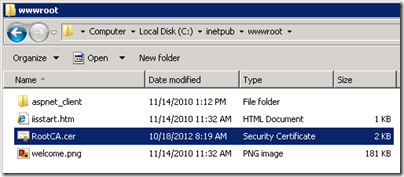
- Copy the newly created certificate text file (e.g. RootCA.cer) file to an accessible web server directory. In this example the default root directory (wwwroot) for IIS on a Windows Server was used. Typically a Lync Server itself cannot be used in this fashion as authentication is required for even HTTP connections to the server, so the default IIS installation on another Windows server was used which allowed for anonymous HTTP connections.
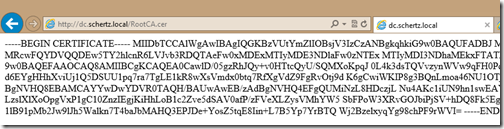
- Test anonymous HTTP access by connecting to the file’s URL (e.g. http://dc.schertz.local/RootCA.cer) using a web browser. The contents of the plain text file should be displayed as shown in the following screenshot.
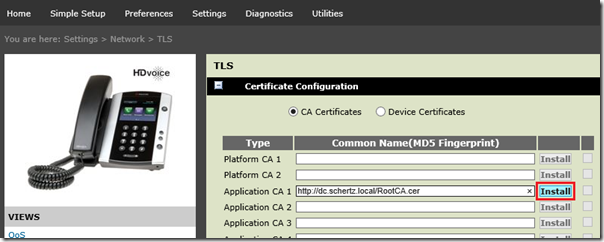
- Open the web management interface and browse to the Settings > Network > TLS menu. Select the desired Application CA container and enter the same URL to the certificate file that was used in the previous step ((e.g. http://dc.schertz.local/RootCA.cer).
- The Install button should activate once a properly formatted URL is entered. Click Install and then device should report that the SSL certificate was successfully installed. If the user credentials were already entered into the device and the Lync Base Profile previously selected then the phone will immediately attempt to register to the Lync Server.
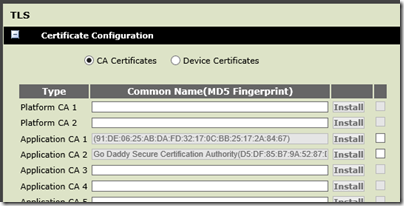
If the certificate authority is multi-tiered, meaning there is a Root CA and one or more subordinate Issuing CA then the entire chain may need to imported into the phone, depending on which CA issued and signed the certificate that was used on the Lync Servers. If loading only the root CA certificate into the device does not resolve the registration failure then try also loading any other CA certificates in the same chain.
Using the web server process previously shown multiple certificates can be imported into separate containers as depicted below.
![image_thumb[6] image_thumb[6]](http://blog.schertz.name/wp-content/uploads/2012/10/image_thumb6_thumb.png)
![image_thumb[10] image_thumb[10]](http://blog.schertz.name/wp-content/uploads/2012/10/image_thumb10_thumb.png)
Is the 4.1 release GA yet. I can't seem to find it on support.polycom.com. I m trying to setup soundpoint IP 321 phone for testing in the lab.
Eric, as mentioned in the other articles the 4.1.0 Lync-only release for the SoundPoint phones can only be provided through your partner, it was not made available for public download. Future releases which support either Lync or Open SIP registration will be provided on the public download pages (like 4.1.2 for the VVX 500). The Lync-only releases are a limited release to prevent the massive amount of existing Open SIP deployments from unknowingly upgrading to a version that is only supported and tested for Lync registration.
I am getting almost the same error except that I am getting this instead of connect error 1
000027.708|sip |4|00|MakeTlsConnection: SSL_connect error 5
000027.708|sip |4|00|MakeTlsConnection: connection failed error -1
Do you have any idea what it means?
Exact same problem here
I'm having the same issue as the gentlemen above. Exported my internal root CA from Lync FE server in Base64 format and imported it in my VVX500 web interface in Application CA 1. Seeing the same messages in diagnostic logging.
0113014747|sip |4|00|MakeTlsConnection: SSL_connect error 5
0113014747|sip |4|00|MakeTlsConnection: connection failed error -1
If you have more than 1 certificate in your root chain you should import all of them into separate slots in the phone.
How do you import for a CX600 or CX500?
You'll need to import the additional root certificate(s) directly into the Lync web services as covered in this article: http://ocsguy.com/2012/05/19/lync-phone-edition-c…
I am unsuccessful at browsing to the phone's IP address.
Can you provide instructions?
I tried http, https.
What am I missing?
It's as simple as entering the phone's IP address in a browser, and both HTTP and HTTP connections are supported, so you may have a network connectivity issue or bad firmware and/or phone.
Sometimes if you have a very modern browser and very old phone firmware you can use compatibility mode to get the web page to show up or respond…
Hi,
I get the following error in my SoundPoint IP 331 phone with Lync Server 2013. Users cannot register into Lync.
0704112527|sip |4|03|CTcpSocket::TlsListenThread: SSL_get_error Error code=5
0704112527|sip |4|03|TLS Listen Thread Exit
0704112527|sip |5|03|Send SSL_get_error nLen -1 nError 5 = error:00000000:lib(0):func(0):reason(0)
0704112633|cfg |4|03|Prov|Unknown suboption received for DHCP option 43
My firmware details are as below.
UC Software Version 4.1.1.0260
BootROM Software Version 5.1.0.85063
The problem is that this does not happen in the previous firmware (4.1.0.84959).
Thanks in advance.
Can't say why that is happening, I suggest you open a support ticket.
Hi Jeff
I've been on this issue for a day or two now. Ever since we had to remove an expired digicert root cert this weekend and run the util to ensure all new root certs are added, we have had issues. Our CX3000's were simple enough to fix, running a hardreset removed the cached root cert chain and they now auto discover fine.
The cx5500, new or old, or factory reset still have an issue. I have tried the steps above and imported the entire root chain manually and still receive the error below. We did not get the certificate issue you have above, but have always had the same error listed in our logs below. Any pointers would be great!
0730181429|so |4|03|[soRegistrationC] Login Credentials valid causing SoRegEventLine Changed
0730181429|cfg |4|03|Prov|Unknown suboption received for DHCP option 43
0730181429|cfg |4|03|Prov|Unknown suboption received for DHCP option 43
0730181430|sip |*|03|dhcpOption120LyncQuery
0730181430|utilm|4|03|uBLFUnCompressed: File /data/polycom/ffs0/Config/Local/WebTicket/0/certProvSvc.mex doesn't exist or is empty
0730181430|app1 |*|03|SoRegistrationEventLineChanged – success lineIndex 0 RegListSize 0
0730181430|app1 |*|03|SoRegistrationEventLast – new AppRegLineC, Default user
0730181430|tickt|5|03|soWebticketGetAllUserInfo: soWebTicketServersGet Failed
0730181430|sip |*|03|Sip Register Usr:CX5500 Dsp:CX5500 Auth:'Using Login Cred' Inx:0
Thanks in advance!
Is this issue resolved? I'm not sure why the CX5500 would be stuck on the old, expired certificate.
Good afternoon, I have been working all week to get the Pin Authentication working on our VVX 500s. I have followed this and several of your other blog posts to get us to where we are now. I can authenticate with user credentials fine on the device but the Pin fails and one of the messages we receive from the phone logs is : /ffs0/Config/Local/WebTicket/0/certProvSvc.mex doesn't exist or is empty. As well as the GetRootCertChain failed. I am at a loss as to where to go from here.
Nathan, does PIN Authentication work on any Lync Phone Edition devices (assuming you have some)?
No. The only other phones we have are 2 Cx600’s, which we paired via USB, a majority of the phones that are deployed are the vvx 500’s. In the past we simply used the Web interface to program the VVX’s. The need has come up to have the Pin authentication working since our client has multiple offices their staff rotate through.
here is the log from our most recent test:
1117125737|cfg |5|00|Prm|Parameter reg.x.auth.useLoginCredentials requested type 2 but is of type 7
1117125737|cfg |4|00|Web|[cfgSaProcessRequestC::signInToLync] Successfully updated the PIN Auth Login credentials
1117125737|so |4|00|[soRegistrationC] Login Credentials valid causing SoRegEventLine Changed
1117125739|app1 |*|00|SoRegistrationEventLineChanged – success lineIndex 0 RegListSize 0
1117125739|app1 |*|00|SoRegistrationEventLast – new AppRegLineC, Default user
1117125741|sip |*|00|dhcpOption120LyncQuery numList [1]
1117125741|utilm|4|00|uBLFUnCompressed: File /ffs0/Config/Local/WebTicket/0/certProvSvc.mex doesn’t exist or is empty
1117125741|utilm|4|00|uBLFUnCompressed: File /ffs0/Config/Local/WebTicket/0/certProvSvc.mex doesn’t exist or is empty
1117125741|tickt|5|00|soRootCertGet: couldn’t get the GetRootCertChainURL
1117125741|tickt|5|00|soWebticketGetAllUserInfo: soWebTicketPinAuthGetRootCertChain Failed
1117125741|sip |*|00|Sip Register Usr:VVX500 Dsp:VVX 500 Auth:’Using Login Cred’ Inx:0
1117125741|cfg |5|00|Prm|Parameter genband.E911.registration.line requested type 2 but is of type 0
Nathan,
10 months later, we are seeing the exact same error. How did you resolve the issue?
MA
Bryan
Hi Jeff. Have you got any guides on configuration of device certificates via provisioning server (for purposes of 802.1x authentication with Lync)?
TIA
Dave
No that is not a topic I’ve tackled yet. There is an official Polycom guide for that: http://support.polycom.com/global/documents/support/technical/products/voice/802_1X_TB57352.pdf
Hi Jeff,
i have the same issue of root CA not trusted , but scenario is different the phones worked fine for more 2 years now and now we changed internal Root CA infrastructure and use new PKI servers and after requesting certificate to all Lync Front End servers from new CA , VVX 400 phones didn’t add new Root CA and did not working.
manual import of new CA working fine but not an option as we have more that 2000 phone. but we can use our IIS provisioning server to deploy that.
why the phone didn’t add new root CA or even replaced old CA with new root CA ?
thanks
After Install my RootCA from my local CA Server,
But username mismath when polycom device contact to My radius server,
How to install device certificate manually
I’ve been unsuccessful in getting a VVX 501 connected to my on prem SfB environment and a test cloud account. It’s at the latest firmware version. I can, however, get Polycom Trios connected.
I noticed the cert order on the Trios is different – the CA cert is in the Application CA 6 field with subordinate certs moving up the list, where on the VVX 501, the CA cert is in the Application CA1 field with subordinates moving down the list. I found it strange that the order is different, but so far it’s the only thing I see different between the two.
The order should not matter. Certificates downloaded in-band from a server are typically placed into the CA6 container, but they will work in any.
Interestingly, by setting the password via the webpage only.. i get this:
21:36:57.215 192.168.20.51 local0.info Apr 17 21:36:56 192.168.20.51 0417213656|copy |*|03|Server ‘ucs.domain.com’ said ‘0004f2fa8aa1-app.log’ is not present
21:36:57.237 192.168.20.51 local0.error Apr 17 21:36:56 192.168.20.51 0417213656|log |4|03|UtilLogC::uploadFifoLog: upload error. protocol 0 result = -1
21:36:57.240 192.168.20.51 local0.error Apr 17 21:36:56 192.168.20.51 0417213656|log |4|03|UtilLogC: Upload succeeded. (ConsecutiveFailures 1 Total 1 MsgSendErr 0)
21:37:17.964 192.168.20.51 local0.error Apr 17 21:37:16 192.168.20.51 0417213716|sip |4|03|TLS-DSK: Setting of Client Certificate failed due to (33558531) error:02001003:system library:fopen:errno = 0x3
21:37:18.035 192.168.20.51 local0.error Apr 17 21:37:16 192.168.20.51 0417213716|sip |4|03|TLS-DSK: Setting of Client Private key failed due to (537346050) error:20074002:BIO routines:FILE_CTRL:system lib
21:37:18.040 192.168.20.51 local0.error Apr 17 21:37:16 192.168.20.51 0417213716|utilm|4|03|uBLFUnCompressed: File /ffs0/Config/Local/WebTicket/0/sip.usr doesn’t exist or is empty
21:37:19.924 192.168.20.51 local0.info Apr 17 21:37:16 192.168.20.51 0417213716|app1 |*|03|Ctx [0] Registered [true]
21:37:20.156 192.168.20.51 local0.error Apr 17 21:37:16 192.168.20.51 0417213716|utilm|4|03|uBLFUnCompressed: File /ffs0/Config/Local/WebTicket/0/sip.usr doesn’t exist or is empty
21:37:20.163 192.168.20.51 local0.crit Apr 17 21:37:16 192.168.20.51 0417213716|wdog |5|03|[utilDeferWatchDog] Deferring watchdog by :240000msec, magicNumber:12123
21:37:20.891 192.168.20.51 local0.error Apr 17 21:37:18 192.168.20.51 0417213718|utilm|4|03|Failed to Convert MicroSoft Dial plan:
21:37:20.897 192.168.20.51 local0.error Apr 17 21:37:18 192.168.20.51 0417213718|utilm|4|03|Failed to Convert all the MicroSoft(Lync) Dial plans
21:37:21.563 192.168.20.51 local0.info Apr 17 21:37:18 192.168.20.51 0417213718|cfg |*|03|Prm|Call Server configuration: Value “sip:basement.meeting.room@domain.com;opaque=app:voicemail” for configuration parameter msg.mwi.1.callBack is longer than the maximum 64, ignoring.
21:37:22.012 192.168.20.51 local0.error Apr 17 21:37:19 192.168.20.51 0417213719|utilm|4|03|Failed to Convert MicroSoft Dial plan: ^0(800\d{6,7}
21:37:22.017 192.168.20.51 local0.error Apr 17 21:37:19 192.168.20.51 0417213719|utilm|4|03|Failed to Convert MicroSoft Dial plan: ^0(8\d{7}
21:37:22.025 192.168.20.51 local0.error Apr 17 21:37:19 192.168.20.51 0417213719|utilm|4|03|Failed to Convert MicroSoft Dial plan: ^0(01111
21:37:22.031 192.168.20.51 local0.error Apr 17 21:37:19 192.168.20.51 0417213719|utilm|4|03|Failed to Convert MicroSoft Dial plan: ^0(1[1-9]\d{7,8}\d{7}
21:37:22.039 192.168.20.51 local0.error Apr 17 21:37:19 192.168.20.51 0417213719|utilm|4|03|Failed to Convert MicroSoft Dial plan: ^45464\d)))\d*(\D+\d+)?
21:37:22.046 192.168.20.51 local0.error Apr 17 21:37:19 192.168.20.51 0417213719|utilm|4|03|Failed to Convert MicroSoft Dial plan: ^0(2[03489]\d{8}\d{7}
21:37:22.054 192.168.20.51 local0.error Apr 17 21:37:19 192.168.20.51 0417213719|utilm|4|03|Failed to Convert MicroSoft Dial plan: ^45464\d)))\d*(\D+\d+)?
21:37:22.062 192.168.20.51 local0.error Apr 17 21:37:19 192.168.20.51 0417213719|utilm|4|03|Failed to Convert MicroSoft Dial plan: ^0(3[0347]\d{8}\d{7}
Hi jeff,
can you help me please?
i use polycom vvx 500, i don’t able to import a root CA (AD PKI): i have this message ” the download file SSL failed”
So i have already configured the 802.1x on my network (PC+Phones, switch h3C, windows server 2012 r2) , the PC can communicate with the server but not the polycom phones. have you any idea please?
Bara