Continuing from Part 1 of the series this article covers the installation and configuration of the Lync Server components on a Standard Edition Front End server. As with the previous article any mandatory steps are identified by bulleted paragraphs while additional steps for validation and knowledge transfer are optional.
Install Lync Server System
The next step is to install a second SQL Express named instance called RTCLOCAL on the local server which will contain a replica of the existing RTC named instance.
Only the first Standard Edition server in the organization would contain the authoritative RTC instance installed in the previous article, while all other Lync Front End Servers (and even Edge Servers) would contain their own RTCLOCAL instance to replicate the Central Management Store data. This approach also allows for redundancy and availability features which were lacking in previous versions of OCS. This RTCLOCAL instance can only ever be stored in an automatically installed SQL Express instance, it is not supported to locate this data in a full SQL Server instance on a Standard Edition server installation.
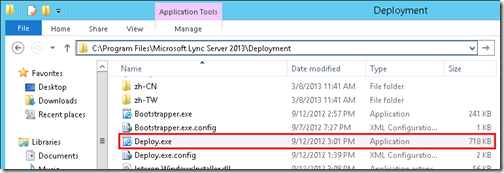
As the Administrative Tools have already been installed on the server then the Lync Server 2013 Deployment Wizard can be found in the Start Menu on the local server. The Lync Server installation media is no longer required as the installation files have been copied to the server in the following default directory.
%ProgramFiles%\Microsoft Lync Server 2013\Deployment
- On the Windows Start Menu search for ‘Deploy’ to locate and launch the Lync Server 2013 Deployment Wizard. From the main menu select Install or Update Lync Server System.
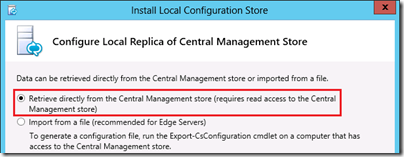
- On Step 1: Install Local Configuration Store select Run and leave the default setting of Retrieve the configuration data directly from the Central Management Store and complete the wizard.
Reviewing the results in the execution window should confirm that the second SQL Express instance of RtcLocal was installed as well as the core Lync Server components.
Checking prerequisite PowerShell…prerequisite satisfied.
Checking prerequisite WindowsIdentityFoundation…prerequisite satisfied.
Checking prerequisite SqlInstanceRtcLocal…installing…success
Checking prerequisite VCredist…prerequisite satisfied.
Checking prerequisite SqlNativeClient…prerequisite satisfied.
Checking prerequisite SqlClrTypes…prerequisite satisfied.
Checking prerequisite SqlSharedManagementObjects…prerequisite satisfied.
Checking prerequisite UcmaRedist…prerequisite satisfied.
Installing OcsCore.msi(Feature_LocalMgmtStore)…success
Secondly the Local CMS replica was instantiated by importing the configuration from the existing CMS database an then replicating the database data itself.
Import-CsConfiguration -FileName "C:\Users\ADMINI~1.SCH\AppData\Local\Temp\2\CSConfigData-2013_03_16-08_10_01.zip" -Verbose -LocalStore
> Enable local replica service
Enable-CSReplica -Verbose -Confirm:$false -Report "C:\Users\administrator.SCHERTZ\AppData\Local\Temp\2\Enable-CSReplica-[2013_03_16][08_08_59].html"
An additional step is performed here which is new to Lync 2013: the automatic replication of certificates to the CMS. Although no certificates have been installed yet for this deployment had there been one then this action would have replicated any existing OAuth certificates required for server to server MTLS communications in Lync Server 2013.
> Replicate-CsCmsCertificates
Logging status to: C:\Users\administrator.SCHERTZ\AppData\Local\Temp\2\ReplicateCMSCertificates-[2013_03_16][08_08_59].html
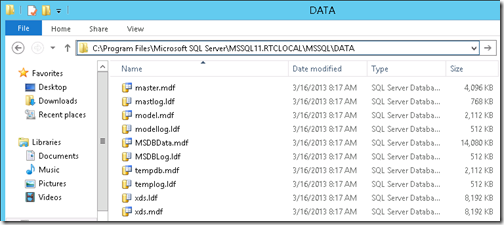
To confirm the installation location of the RTCLOCAL database files on the server check the default SQL Server installation directory for the existence of the xds files.
%ProgramFiles%\Microsoft SQL Server\MSSQL11.RTCLOCAL\MSSQL\DATA
- On the Lync Server 2013 Deployment Wizard advance to Step 2: Setup or Remove Lync Server Components and click Run to start the Set Up Lync server Components wizard.
Once again the Bootstrapper application will execute and perform a prerequisite check before installing additional components. These include a third SQL instance called LyncLocal and additional Windows Speech components and foreign language packs.
Checking prerequisite SqlSharedManagementObjects…prerequisite satisfied.
Checking prerequisite UcmaRedist…prerequisite satisfied.
Checking prerequisite WinFab…installing…success
Checking prerequisite MicrosoftIdentityExtensions…installing…success
Checking prerequisite SqlInstanceLyncLocal…installing…success
Checking prerequisite SqlInstanceRtc…prerequisite satisfied.
Checking prerequisite RewriteModule…installing…success
Checking prerequisite SpeechPlatformRuntime…installing…success
Checking prerequisite MSSpeech_TTS_ca-ES_Herena…installing…success
Checking prerequisite MSSpeech_TTS_da-DK_Helle…installing…success
Immediately following will be the installation of the Lync server components which make up the different services and roles on the Front End server (e.g. AVMCU, Mediation Server).
Installing OcsMcu.msi(OcsMCUCommon, ASMCU, AVMCU, IMMCU)…success
Installing AppServer.msi(Feature_AppServer)…success
Installing Ats.msi(Feature_Ats)…success
Installing CPS.msi(Feature_CPS)…success
Installing DataMcu.msi(Feature_DataMCU)…success
During the WebComponents installation a number of features will be installed which are the different virtual web directories and application pools in IIS.
Installing WebComponents.msi(Feature_Web_Common, Feature_Web_External, Feature_Web_GroupExpansion_Ext, Feature_Web_HybridConfig_Ext, Feature_Web_Internal, Feature_Web_JoinLauncher_Ext, Feature_Web_JoinLauncher_Int, Feature_Web_LocationInfo_Int, Feature_Web_Lwa_Ext, Feature_Web_Lwa_Int, Feature_Web_Mcx_Ext, Feature_Web_Mcx_Int,
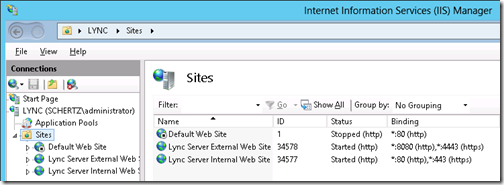
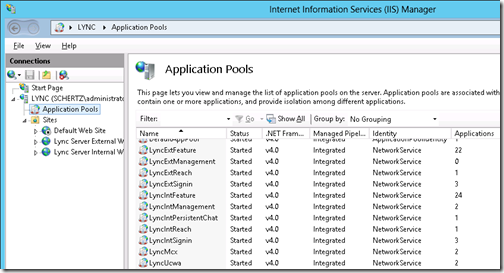
To confirm the installation and configuration of the various web services launch Internet Information Services Manager (inetmgr.exe) and browse to the Sites folder to see the status of the two new web sites.
Then select the Application Pools object to view the various Lync web services which were installed for both the internal and external web sites.
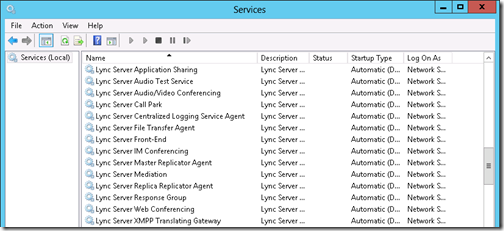
Also check the installed services by running the Services control panel applet (services.msc). They will not yet be running as server certificates must be imported first, which is the next step in the deployment.
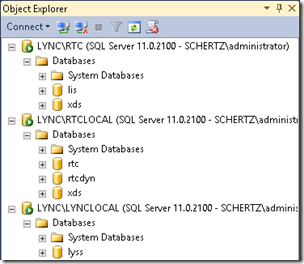
To review exactly what SQL instances were installed and their roles the Microsoft SQL Server Management Studio (if installed as covered in the previous article) can be used to view each instance and database.
Instance Database Description RTC lis Location Information Services data RTC xds Central Management Store data RTCLOCAL rtc Standard Edition Pool data RTCLOCAL rtcdyn Standard Edition transient user data RTCLOCAL xds Local replica of Central Management Store data LYNCLOCAL lyss Lync Storage Service data
Returning to the server deployment process the next step is to request and assign server certificates so that the Lync services can be started.
- Run Step 3: Request, Install or Assign Certificates and then expand the Default Certificate entry to verify that all roles are checked. Click Request to start the Certificate Request wizard and enter the information listed in the following tables.
Delayed or Immediate Requests
- Send the request immediately to an online certificate authority
Choose a certificate Authority
- Select from a list detected in your environment
(DC.schertz.name\schertz-RootCA)
Certificate Authority Account
Skipped as the current Administrator account has sufficient permissions to perform this action.
Specify Alternate Certificate Template
Skipped as the Windows CA certificate template of ‘Web Server’ will be used by default.
Name and Security Settings
Friendly Name Lync Front End Cert Bit Length 2048
- ”Mark the certificate’s private key as exportable”
Organization Information
Organization Schertz Lab Organizational Unit Home
Geographical Information
Country/Region United States State/Province Illinois City/Locality Chicago
Subject Name / Subject Alternate Names
The following names will be automatically populated for the subject name and subject alternative name.
Subject Name lync.schertz.name Subject Alternative Name lync.schertz.name
dialin.mslync.net
meet.mslync.net
admin.mslync.net
Lyncdiscoverinternal.mslync.net
Lyncdiscover.mslync.net
SIP Domain setting on Subject Alternate Names (SANs)
Configured SIP Domains mslync.net
Configure Additional Subject Alternate Names
Skipped as no additional SIP domains are configured in the topology so there are none to add to the certificate request.
Completing the process will execute the Request-CsCertificate cmdlet with the provided configuration information, performing an online certificate request against the CA and then automatically importing the issued certificate into the Local Computer store. (The following results were snipped down to just the important items.)
> Request Certificate
Request-CSCertificate -New -Type Default,WebServicesInternal,WebServicesExternal -CA "DC.schertz.name\schertz-RootCA" -Country US -State "Illinois" -City "Chicago" -FriendlyName "Lync Front End Cert" -KeySize 2048 -PrivateKeyExportable $True -Organization "Schertz Lab" -OU "Home" -DomainName "sip.mslync.net" -AllSipDomain -Verbose -Report
Create a certificate request based on Lync Server configuration for this computer.
Issued thumbprint "C6D87D6224A91E103734C582034E7FBE22F46A4A" for use "Default,WebServicesInternal,WebServicesExternal" by "DC.schertz.name\schertz-RootCA".
No changes were made to the Central Management Store."Request-CSCertificate" processing has completed successfully.
- In the next window verify that Assign this certificate to Lync Server certificate usages is selected and then click Finish to launch the Certificate Assignment wizard next.
- Complete the wizard which automatically runs the Set-CsCertificate cmdlet to assign the desired certificate to the three server usages.
> Assign Certificate
Set-CSCertificate -Type Default,WebServicesInternal,WebServicesExternal -Thumbprint C6D87D6224A91E103734C582034E7FBE22F46A4A -Confirm:$false -Report
The following certificate was assigned for the type "Default":
Default: C6D87D6224A91E103734C582034E7FBE22F46A4A lync.schertz.name 03/16/2015 CN=schertz-RootCA, DC=schertz, DC=name 5A0000000313D2DB08C6C90DCE000000000003The following certificate was assigned for the type "WebServicesInternal":
WebServicesInternal: C6D87D6224A91E103734C582034E7FBE22F46A4A lync.schertz.name 03/16/2015 CN=schertz-RootCA, DC=schertz, DC=name 5A0000000313D2DB08C6C90DCE000000000003The following certificate was assigned for the type "WebServicesExternal":
WebServicesExternal: C6D87D6224A91E103734C582034E7FBE22F46A4A lync.schertz.name 03/16/2015 CN=schertz-RootCA, DC=schertz, DC=name 5A0000000313D2DB08C6C90DCE000000000003
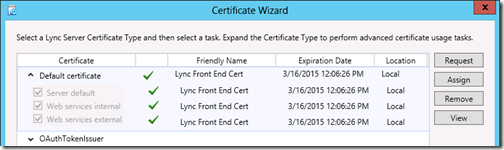
At this point the main Certificate Wizard window should reflect the new status by adding a green check mark to the Default certificate and its usages.
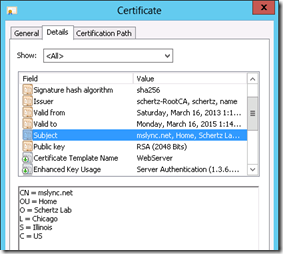
Since this is the first Lync 2013 server in the topology then an additional shared certificate needs to be created for use with a new open authentication standard called OAuth. This certificate will be used for server-to-server communications between Lync 2013 servers in addition to other 2013 products which support OAuth like Exchange Server and Office Web Apps Server.
- On the main Certificate Wizard window expand and highlight the OAuthTokenIssuer entry and click Request to start the Certificate Request wizard and enter the information listed in the following tables.
Delayed or Immediate Requests
- Send the request immediately to an online certificate authority
Choose a certificate Authority
- Select from a list detected in your environment
(DC.schertz.name\schertz-RootCA)
Certificate Authority Account
Skipped as the current Administrator account has sufficient permissions to perform this action.
Specify Alternate Certificate Template
Skipped as the Windows CA certificate template of ‘Web Server’ will be used by default.
Name and Security Settings
Friendly Name Lync OAuth Cert Bit Length 2048
Organization Information
Organization Schertz Lab Organizational Unit Home
Geographical Information
Country/Region United States State/Province Illinois City/Locality Chicago
Subject Name / Subject Alternate Names
The following names will be automatically populated for the subject name and subject alternative name.
Subject Name lync.schertz.name Subject Alternative Name <blank>
Configure Additional Subject Alternate Names
Skipped as no additional SIP domains are configured in the topology so there are none to add to the certificate request.
Completing the process will execute the Request-CsCertificate cmdlet with the provided configuration information, performing an online certificate request against the CA and then automatically importing the issued certificate into the Local Computer store. (The following results were snipped down to just the important items.)
> Request Certificate
Request-CSCertificate -New -Type OAuthTokenIssuer -CA "DC.schertz.name\schertz-RootCA" -Country US -State "Illinois" -City "Chicago" -FriendlyName "Lync OAuth Cert" -KeySize 2048 -PrivateKeyExportable $True -Organization "Schertz Lab" -OU "Home" -AllSipDomain -Verbose -Report
Create a certificate request based on Lync Server configuration for this computer.
Issued thumbprint "2A55DA39DD43DAEB2AC2510AFB61EE21103ADCDB" for use "OAuthTokenIssuer" by "DC.schertz.name\schertz-RootCA".
No changes were made to the Central Management Store."Request-CSCertificate" processing has completed successfully.
- In the next window verify that Assign this certificate to Lync Server certificate usages is selected and then click Finish to launch the Certificate Assignment wizard.
- Complete the wizard which automatically runs the Set-CsCertificate cmdlet to assign the desired certificate to the OAuth usage.
> Assign Certificate
Set-CSCertificate -Identity Global -Type OAuthTokenIssuer -Thumbprint 2A55DA39DD43DAEB2AC2510AFB61EE21AA6ADCDB -Confirm:$false -Report
The following certificate was assigned for the type "OAuthTokenIssuer":
OAuthTokenIssuer: 2A55DA39DD43DAEB2AC2510AFB61EE21AA6ADCDB mslync.net 03/16/2015 CN=schertz-RootCA, DC=schertz, DC=name 5A00000004B92C660018992201000000000004> Export Global Configuration Store
Export-CSConfiguration -FileName "C:\Users\ADMINI~1.SCH\AppData\Local\Temp\2\CSConfigData-2013_03_16-13_27_15.zip"
> Import Local Configuration Store
Import-CSConfiguration -LocalStore -FileName "C:\Users\ADMINI~1.SCH\AppData\Local\Temp\2\CSConfigData-2013_03_16-13_27_15.zip"
> Replicate-CsCmsCertificates
The main difference between the two certificate requests is that the creation of the OAuth certificate also triggers a database replication task as this certificate is automatically replicated to all Lync Servers in the topology.
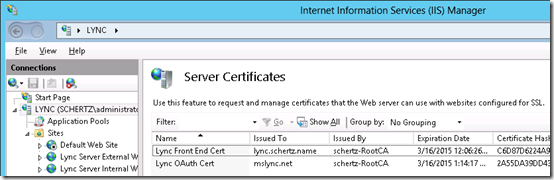
To review the new certificates on the server use either the Certificates snap-in available in the Microsoft Management Console (mmc.exe) or IIS Manager (inetmgr.exe). In IIS Manager for example highlight the server object in the Connections window and then open Server Certificates in the IIS section to view the two Lync server certificates.
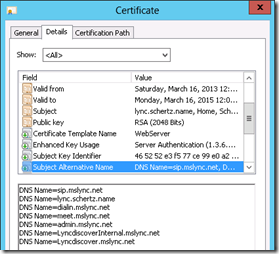
View each certificate file to see the configured parameters and compare the Subject Name and SAN fields (the OAuth certificate will not include any SAN entries).
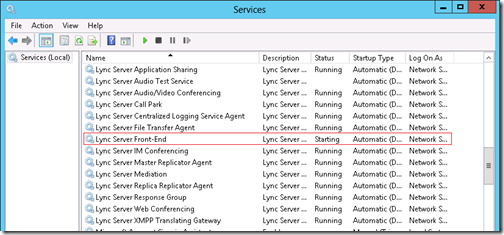
- Returning to the Lync Server 2013 Deployment Wizard move on to Step 4: Start Services and click Run to trigger an automatic start of all Lync services. This process may take a few minutes as due to some service dependencies they are started in a specific order and not all simultaneously.
> Start Services
Start-CSWindowsService -NoWait -Verbose -Report
Start services for the Lync Server computer "lync.schertz.name".
"Start-CSWindowsService" processing has completed successfully.
To verify that all services have started successfully click Run on the Service Status (Optional) step to launch the Services control panel applet. Depending on how soon after the previous step this is performed one or more of the services may still be in a stopped or starting state. (Note that the Lync Server Audio Test Service will typically not be running as this service will routinely start and stop itself.)
If the Lync Server Front-End service (or any other prerequisite service) is still reported as starting then check the server CPU in Task Manager as it may still be fully tasked with all of the first-time processes performed after a fresh server installation.
DNS Configuration
Since this deployment is using a Standard Edition server then the required server host record (e.g. lync.schertz.name) already exists in the form of the Dynamic DNS record created by the server when it was previously joined to the domain. But a number of additional DNS records need to be manually created to match the various Autodiscover and Simple URLs which were defined in the topology in the previous article.
- Review the Subject Alternative Name field on the Default certificate which was just assigned to the Front End server as it will contain all of the FQDNs which need to be represented in the appropriate internal DNS forward lookup zones.
DNS Name=sip.mslync.net
DNS Name=lync.schertz.name
DNS Name=dialin.mslync.net
DNS Name=meet.mslync.net
DNS Name=admin.mslync.net
DNS Name=LyncdiscoverInternal.mslync.net
DNS Name=Lyncdiscover.mslync.net
As mentioned the server FQDN is already automatically defined in the proper DNS zone so that entry can be ignored (e.g. lync.schertz.name). The Simple URLs (dialin, meet, admin) were manually created in the previous article after publishing the topology so all that remains to be created are the Automatic Client Sign-In and Autodiscover records.
It is important to understand the different between the legacy Automatic Client Sign-In process and the newer Lync Autodiscover approach as these are two completely different solutions.
In the legacy scenario OCS 2007 and Lync 2010 clients locate their SIP registrar directly by looking for one or more predefined hostnames (e.g. sip.<sipdomain>). Yet in the newer Autodiscover scenario Lync 2013 clients are programmed to first look for a different set of predefined hostnames (e.g. lyncdiscover.<sipdomain>). But these names will instead direct the client to a web service which will in turn respond back to the client with the appropriate SIP registrar URL. So in the first case the clients are attempting to locate a SIP registrar directly, where as in the second and more flexible solution they are attempting to locate a service which will tell them where to find their SIP registrar. This advancement in Lync provides for additional flexibility not previously made available, most notably the ability to support distributed Access Edge registrations in enterprise networks with multiple Edge pools.
Legacy Automatic Client Sign-In
This section is only required if any legacy clients will be used with the environment (e.g. Lync 2010). All Lync 2013 clients will leverage the newer Autodiscover process, although some 2013 clients still support this legacy mode as a fall-back.
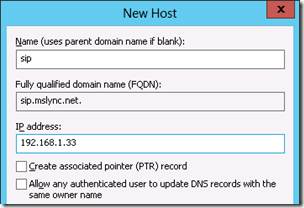
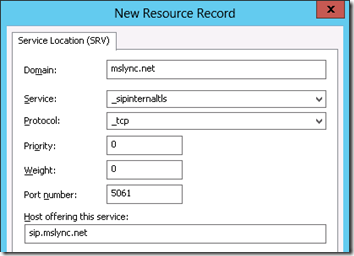
- Using DNS Manager create a new Host (A) record in the DNS zone which matches the SIP domain namespace (e.g. sip.mslync.net) using the same IP address as the Lync Front End server.
- Create a new Service Location (SRV) record in the same zone (e.g. _sipinternaltls._tcp.mslync.net) and define the Port number as 5061 and the Host offering this service as the previously created host record (e.g. sip.mslync.net)
To verify the new DNS record configuration run the following command from the Windows Command Prompt.
C:\>nslookup -q=srv _sipinternaltls._tcp.mslync.net
_sipinternaltls._tcp.mslync.net SRV service location:
priority = 0
weight = 0
port = 5061
svr hostname = sip.mslync.net
sip.mslync.net internet address = 192.168.1.33
Lync Autodiscover
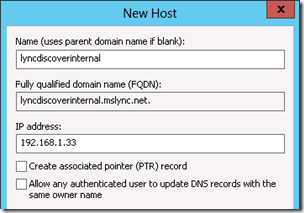
Either a Host (A) or an Alias (CNAME) record can be used for the Autodiscover records. But some Lync clients (primarily the mobility clients) do not support a CNAME record which points to a Host record in a different domain namespace, so in the topology used in this series of articles it would be poor practice to create an alias in the SIP domain namespace (e.g. lyncdiscoverinternal.mslync.net) which then pointed to the server’s FQDN (e.g. lync.schertz.name) in another namespace.
Thus two configuration possibilities are available: either use a Host record with the server’s IP address, or create an Alias record pointing to a Host record in the same namespace (e.g. sip.mslync.net). In an Enterprise Edition deployment this Lyncdiscoverinternal record would typically be an alias pointing to the Internal Web Service FQDN (e.g. lyncweb.<sipdomain>) but as this is a Standard Edition server then in the internal web service FQDN is the same as the server’s FQDN (e.g. lync.schertz.name) so the simplest configuration would be to just create a host record here.
Only the Lyncdiscoverinternal entry should be created on internal DNS zones as Lyncdiscover is used by external clients and thus should be reserved for external DNS zones which will be addressed in a later article.
- Create a new Host (A) record in the DNS zone which matches the SIP domain namespace (e.g. lyncdiscoverinternal.mslync.net) using the same IP address as the Lync Front End server.
Summary
If all has gone according to plan then the environment now includes a functional Lync Front End server which is ready for additional configuration and client testing.
Hi master Schertz. 😉
Just would like to mention that you have misstyped SRV port number. 😉
Indeed. Typo fixed. Thanks for reading already!
Fantastic so far, Jeff. Suggestion: turn this into a "Lync 2013 CU1" deployment series with a final post on updating to CU1 – there were definitely a few quirks with that process that I felt were poorly documented by our friends in Redmond! -Wes
Hi g0b3ars,
So, specifically for the "Lync Server 2013 CU1" deployment, can you give me more detail regarding the quirks / issues regarding updating to CU1? We are always trying to improve / revise the details as we receive feedback.
Hey Jeff, good write up once again. I believe Lync 2010 client now uses Autodiscover as well. http://technet.microsoft.com/en-us/library/gg3987…
Curious of your findings as well regarding 2010 based on that article. Also, where in the docs does it state Mobility doesn’t support CNAMEs pointing to different domains? Is it because I cannot push TrustDataModel to it via GPO? If you can send me that doc in technet that would be useful. I will need that for my current design and I must have over looked that tidbit. Thx man!
Interesting, as when testing a Lync 2010 Windows client with CU7 (.4356) I'm not seeing any DNS requests for lyncdiscover records, only the legacy records. I'll have to dig into this more. Regarding the CNAME question take a look at the last 'Note' on this page: http://technet.microsoft.com/en-us/library/hh6900… starting with the statement "Mobile device clients do not support multiple Secure Sockets Layer (SSL) certificates from different domains. Therefore, CNAME redirection to different domains is not supported over HTTPS".
Awesome thanks. That link is dead but I’m pretty sure I know where it is, I’ll find it, but others may need it to properly redirect. Let me know what you find on 2010. I’m pretty sure when I tested it was showing Lyncdiscover and I was using fiddler to get my eyes on it.
WordPress truncates the text but the embedded link is still good (at least for me).
Jeff. I got another one for you regarding mobility. From technet – “All Mobility Service traffic goes through the reverse proxy, regardless of where the origination point is—internal or external.” I don’t believe this is the case anymore with CU1. In my testing and latest deployment, internal stays internal. The XML document returns both internal and external webservices. Have you discovered the same?
That statement from TechNet doens't sound right to me either, even pre-CU1. The mobile Lync will be directed to register to a web services based on it's location, so if it receives a response from lyncdicoverinternal versus lyncdiscover that is what 'tells' the client where it is located (internal/external). Thus the correct configuration of DNS records is key to routing the traffic to the desired server.
Jeff your Part 1 was easy to follow. I cannot publish my topology. I added the domain admin to the groups you wanted me to and I still cannot publish I get the following
Found "RTCUniversalServerAdmins": True 3/25/2013 11:28:07 AM
└ Found "RTCUniversalConfigReplicator": True 3/25/2013 11:28:07 AM
└ Found "RTCUniversalReadOnlyAdmins": True 3/25/2013 11:28:07 AM
└ TaskFailed: Task execution failed. 3/25/2013 11:28:22 AM Error
└ Error: Cannot open Service Control Manager on computer 'LynServer.SC.LOCAL'. This operation might require other privileges.
► Details
└ Type: InvalidOperationException
└ ► Stack Trace
└ at System.ServiceProcess.ServiceController.GetDataBaseHandleWithAccess(String machineName, Int32 serviceControlManaqerAccess)
at System.ServiceProcess.ServiceController.GetServicesOfType(String machineName, Int32 serviceType)
at Microsoft.Rtc.Common.Data.DbUtils.GetSqlServerStatus(Server sqlServer)
at Microsoft.Rtc.Common.Data.DbUtils.StartSqlServer(Server sqlServer, Action`2 log)
at Microsoft.Rtc.Common.Data.DbSetupBase.ConnectSqlServer()
at Microsoft.Rtc.Common.Data.DbSetupBase.Initialize(Dictionary`2 parameters)
at Microsoft.Rtc.Common.Data.DbSetupBase..ctor(Dictionary`2 parameters, Action`2 log)
└ ► Additional Details
└ Error: The RPC server is unavailable
► Details
└ Type: Win32Exception
└ ► Stack Trace
└
3/25/2013 11:28:22 AM Error
└ TaskFailed: An error occurred while creating or updating the database for feature CentralMgmtStore. For details, see the log file 'C:\Users\administrator.SC\AppData\Local\Temp\2\DbExists-CentralMgmtStore-LynServer.SC.LOCAL_rtc-[2013_03_25][11_28_07].log' 3/25/2013 11:28:22 AM
└ TaskFailedResolution: Consult exception information and previous errors for more information on how to resolve this error. 3/25/2013 11:28:22 AM
└ Error: An error occurred: "System.InvalidOperationException" "Cannot open Service Control Manager on computer 'LynServer.SC.LOCAL'. This operation might require other privileges." 3/25/2013 11:28:22 AM Error
Make sure that you are running Topology Builder as an administrator in the event you are using any account other than the built-in Administrator user account.
Hope the Edge part comes.
I has installed Edge 2013 with old 2010 step.
So far so good now. But not testing yet,hope all ok,
Using a Lync 2013 Edge server should be fine with 2010 Front End servers still in place. Not sure I'm posting an article on Edge Server deployment yet, it's basically identical to 2010 so I'm not sure there is a lot of value in rehashing that here.
did you test this setup . Lync 2010 front end and Lync 2013 Edge server ? I am planning to put this in production.
No, I have not tested that but my initial thought is that it should be fine. Typically the Edge server is upgraded last, but it is not a requirement in 2013.
Trying to get Lync for Mac Office 2011 to work with new deployment of Lync 2013. Keep receiving error on client "Sign in to Microsoft Lync failed because the service is not available or you may not be connected to the internet" cant find logs in Mountain Lion with current documentation. We are a Microsoft shop and don't typically deal with issues of this sort. Works fine with user on windows 7 and 8 with Lync 2013 Client. Any help or if this is even possible.
Figured it out. had to hard code client with lyncserver.domain.local:5061 and client signed in. still not sure what DNS record I need to create to make sign in from mac client automatic. hope this will help someone.
The Mac clients do not utilize Lyncdiscover so they still need the legacy Automatic Sign-In records (SRV/Host) to be configured.
Part 3 Link is dead…
Not dead, just not born yet 🙂 Coming soon…
When is Part 3 going to be available?
My plan is post it before the end of the month, but it's not completed yet.
Jeff. I have a lab setup and we are looking to setup the edge server (lync 2013). I only am using a single edge server and have only 1 FE server. So my questions are.. 1. Do I need to do any load balancing since there is only 1 edge server and 1 front end pool? My ASA firewall does not support DNS load balancing so am I forced to do HW load balancing, and if so back to question 1 what is the need for load balancing if I only have 1 edge and front end server. 2. Do you have to have 2 NICs on an edge server?
When there is a single server in a pool then no load balancing is required. And yes, the Edge serve must have separate internal and external interfaces.
Hi jeff,
I am testing my Lync 2013 mobile client and I want to know if I need an edge server for Lync Mobile services.
Do A/V between two Lync Mobile Client use Edge during their Lync sessions.
Thanks in advance
I don't know if anyone has tested the actual behavior without, but I would doubt even P2P calls between mobile clients on the same network would function. The Edge server is required for all external media scenarios and not having one in the deployment would most likely prevent external clients from even attempting to negotiate media. In scenarios where media would need to traverse firewalls and address translation there is no possible way that could work.
Hi Jeff,
I have migrated Lync from 2010 to 2013 and one day all of a sudden my edge is no longer replicating with Front end. Could you please tell me where to start ? Some ppl told me it might be related to firewall rules but I have disabled firewall internally.
Lync FE can resolve Edge and edge can ping the FQDN of FE. I have no idea where to start.
Thanks
Topology data replication is over the same port in Lync 2013 as it was in 2010 (push from Front End to Edge over 4443).
Hello Jeff,
Create article! Have you covered any on using exchange 2013 for voice mail for Lync 2013. I'm trying to get it to work but having a few issues.
Brenton,
I haven't had time to write this article yet but it's on my to-do list.
Do I need an edge server to be able to login to lync when im out of office or can I just open the ports to the standard edition server?
For a supported external user scenario: yes. If you want to can simply forward port 5061 from the Internet to your Front End server but (a) this is unsupported and insecure and (b) you'lll only be able to sign-in with some clients (mobility clients will not work for example) and only IM/Presence will function. All other capabilities (web conferencing, audio/video calls, etc) will not work without an Edge Server.
Hi Jeff,
I have a question do the Lync client share desktop or programs to HDX (RTV enabled).
Regards,
Arun
No, a Polycom RMX, DMA, and CSS core deployment would be required to provide a bridge between standards-based content sharing and Lync clients.
Hi Jeff,
We've upgraded from Windows Server 2008 R2 DC / CA to Windows Server 2012 DC / CA. My question / problem is : after upgrading , do I have to recreate default certificates and OAuth certificates for Lync Server 2013? so What exactly need to do? please clarify. thanks in advance.
If you've replaced your certificate authority then you would need to reissue all certificates, but if the CA is still available and no certificates were revoked then you don't have to. It would be recommended to update them all in most cases, if you can.
Hi Jeff, any word on part 3? These two articles have been INCREDIBLE by the way! Thanks for your hard work!
Michael, Part 3 is about halfway complete but I probably won't have it posted until after TechEd.
Q. I am puzzled by all the different and partially misleading info about LYNC certs that are required. So this is the scenario: Single Lync STD Server (lyncsrv.abc.local); Single Edge(LyncEdge); TMG for publishing. Internal AD name ABC.local; External (public) domain name ABC.com.Sip name ABC.com; meet, dialin, webconf, av,
I need to prepare the cert-reg files for external CA. How many certs should I request (from internal CA and from Public CA), which one goes where, for which LYNC server adapter/role and what is the finite list of names that should be included in each of the certs ?? I plan on requesting separate single name certs for EDGE. HELP Please !!!
In most cases you should be requesting a single certificate for the Front End server and two certificates for the Edge Server (internal and external facing). The reverse Proxy depends on the configuration but typically all FQDNs can be placed in the same certificate and used across multiple listeners if needed. The names depend on your configuration but the Certificate Wizard should get you most of the way there.
Hi and thank you for the articles. I tried to go to the Part 1 link but it seems to broke.
Link is fixed. Thanks for the heads-up.
Hi Jeff and thanks for the great articles.
I've several questions to ask you.
1. According to my situation, my edge server have 2 NICs, and they are in same subnet./192.168.0.x,y/ Is it ok?
2. Do I need to buy public certificate(for example- from godaddy) to my edge and front ends? Without public cert, is it possible to access to my edge server from mobile phone?
3. I've deployed my servers with domain.local domain. But to access to lync from my mobile externally(with 3G or WiFi), I need public domain like domain.com right? Do I need get write sip.domain.com to public IP by my external dns provider?
Thank you so much.
Placing both interfaces in the same subnet is not recommended and is unsupported by Microsoft. The Edge Server should be using public certificates on the external interface, and internal certificates on the internal interface. You can use either on the Front End server depending on the overall configuration and requirements you have. I suggest reading through my other articles on this topic for more detailed guidance: http://blog.schertz.name/tag/certificates
thanks for you urgent reply.
My case is for testing purpose only. "Not recommended" doesn't mean it doesn't work right?
Also is it possible to get consulting from you? for a real deployment.
'Not recommended' doesn't necessarily mean it will not work, but results and behavior might be less than desirable. Really it means that you are on your own 🙂
hello again Jeff,
I've deployed reverse proxy, edge and front-end.
reverse proxy and edge external interface using same public CA. (CN=sip.contoso.com SANS: contoso.com, lyncdiscover.contoso.com, extweb.contoso.com)
edge internal interface is using internal CA. (CN=edge.contoso.local)
front-end's default, internal, external interfaces are using same cert from internal CA. (all related names are included, no idea that public dns names included such as lyncdiscover.contoso.com)
It's works in internal domain joined pc's. But can't connect external pcs and mobiles. http://technet.microsoft.com/en-us/library/gg4296… – link testing doesn't work. It says : The website cannot be found.
I've used http://www.testocsconnectivity.com and port 5061 succeeded, but no success on 443 and mobility.
When I browse localhost/meet and localhost/dialin it works, but not works on from externally like extweb.contoso.com/meet extweb.contoso.com/dialin.
Is it problem with Reverse proxy? or it is with front end IIS?
Great post!!
How did you plan backup/restore and DR for this Lync 2010/2013 Lab Setup?
For my labs I periodically just export my Hyper-V guests to another disk to grab a point-in-time snapshot of the entire environment.
Just a short Question
After installing Lync Standard Server, when adding DNS Names:
DNS Name=sip.mslync.net
DNS Name=lync.schertz.name
DNS Name=dialin.mslync.net
DNS Name=meet.mslync.net
DNS Name=admin.mslync.net
DNS Name=LyncdiscoverInternal.mslync.net
DNS Name=Lyncdiscover.mslync.net
Each one (SAN Name in the certificate) a new A record in DNS (pointing to the standard Server?
Or which type of DNS entry I have to use?
best regards from Germany
Lutz
This is covered throughout both articles; you can use Host (A) or Alias (CNAME) records for some of these, while others must be Host only. The official TechNet documentation also covers this. I typically use Host records for all of these, but will often use CNAME records for others.
Than you very much, very nice articles, as always.
I don't know what I did wrong, but when I did the Lync OAuth Cert, I was prompt with the external domain (.net) instead on the internal one (.name). Does it matter ? Front end cert was OK out of the box.
Waiting for part 3!
Thank you Jeff for your posts , really helpfull
When you will write 3 part about configuration ?
best regards from Uzbekistan
I have a draft near completion but have been working on other things lately. Hoping to post this at some point.
Awesome as always Jeff thanks for this hope you are well 🙂
Second or third on Part 3….
Yeah, things have been quite busy for me both in and out of work lately. My lab is also about to be torn down as I'm moving soon so it'll be a few months until I can get back to the detailed deployment articles.
Jeff,
I don't know how to thank you. It has been three crazy days for me in trying to implement Lync 2013. I finally got it right thank to your post and blog. Great Job.
Basil
Awesome articles, thanks!!! Is there a part 3?
Best regards, Magnus, Sweden
One of these days when I get more time I may post more in this series.
Hi Jeff,
I understand this is a bit off topic here, Just wondering if you are aware of a free app or tool that can be used to deploy a console at receptionist’s desk to she can see everyone’s presence.
While I am not looking for very sophisticated solutions like these guys have but something in similar fashion.
Examples are Slide 11 or 12 http://www.slideshare.net/ucexpo/microsoft-lync-2…
or Page 2 http://www.enghouseinteractive.co.uk/wp-content/u…
Sorry, I'm not aware of anything like that.
Hey Jeff,
Parts 1 and 2 looking real good. Looking at the post date of part 2 though…. is this series dead?
Arjan, at this point in Lync 2013's life-cycle I don't see a lot of value in adding more sections to this series, given that these take a lot of time and testing to produce. I'll probably wait until the next version of Lync is released to do more of these.
Hi Jeff,
if our SIP domain is something.COM and our internal AD domain name is something .NET .. .Internal AD DNS would be something.NET and we have something.COM hosted on public DNS servers.
is there any way to create the automatic internal SRV DNS records on the internal AD servers? Since our SIP domain is something.COM I cannot create the _sipinternaltls._tcp.something.COM … b/c the root of the forward lookup zone is something.NET
I need to have split-brain DNS setup so that you also have an internal DNS zone for your public ".com" namespace. This is basic Active Directory DNS best practice and should be part of your overall AD design.
Hi Jeff,
I too would like to see an continuation of this series – I know you have the Lync 2010 Part 3 and 4, but are there any differences with Lync 2013? Or possible a series based on Enterprise deployment.
Cheers
Chris
Oh – I have just seen your responses WRT Lync lifecycle in other posts. Shame.
We certainly need more of this Lync Deployment series.
At this point in the product’s life-cycle I will most likely wait until the next release of Lync to revisit these very time-consuming deployment articles. Also, there are already a host of Lync 2013-related deployment articles online provided by other Lync MVPs.
Hello Jeff,
First I wanna say thank you for this great deployment articles.
Secondly, I have a question about Simple URLs.
We in our company have two Lync Front-End Pools (one for HQ and one for Germany). So far so good, communication between those two works fine. And I can create a Meeting from within Lync.
But I cannot start a Lync Meeting via Outlook, only the guys from HQ can.
The Simple URL for meeting is poiting to the HQ Lync Front-End Server.
Do we need to create a DNS Pool for Meetings? Or have we forgotten any option to be set that the communication works?
The guys from HQ can join any Outlook meeting (even created from German user pool). It must be possible that we can join and create Lync Meetings from our "german" user pool, too, shouldn't it?
Thanks for assistance and excuse my language since I am not a Native Speaker.
That should work but I don't have any guesses as to why it is not; you need to figure out errors the client is receiving when it cannot join.
Hi Jeff / All,
I'm confused about making the internal dns SRV record. Let's say we have a Active Directory domain : domain.name. Our Active Directory servers are resolving domain.name records. But our external domainname is domain.com.
For the neccesary A records, I can make a new zone, for example, meet.domain.com (not the zone whole zone : domainm.com,). How to do this with a SRV
record for domain.com ? If we add the zone domain.com it will try to resolve all *.domain.com. And this is not good, because domain.com also have other dns records on the public dns servers that will resolve to public ip addresses.
That is a standard DNS Split-Brain topology where you should have separate DNS servers internal and external with different sets of records for the same namespace. This design prevents exposing private IPs to the Internet and directs Lync clients to the proper servers based on their location. Having a single DNS server resolve all requests, internal and external, for the same namespace is poor practice and Lync is not the only product which can run into problems with that type of design.
Hi Jeff,
Is it confirmed that we can't use an internal certificate (windows 2012 r2) on our lync external edge interface
or it should be from 3rd party approved Microsoft CA
Correct. Using an internal private certificate on the external Edge is unsupported. Your test environments you can use one for partial connectivity.
Hi Jeff,
We have deployed Lync 2013 pilot for our company and so far everything works fine, except for login to Web App/Scheduler/Dialin web page
our domain is setup in child/parent topology, all of Lync accounts are configured to login using username@parent.com
However, we will need to use domainusername to login to web schedulerdialin, which I had tried childusername, parentusername to login and both were not working. Is there anything that I was missing during the setup here? Thanks
Hello Jeff,
I’m just trying out Lync and was wondering if you know how I can test it without having any certificates. I’ve followed your guide up until the certificates part. Great article.
You need to have some trusted SSL certificate as TLS and MTLS are required in the Lync environment. You can get free trial certificates from some of the popular third party certificates authorities, just make sure they are issued by a trusted CA or you’ll need to manually load those trial CA certificates chains. I would also recommend to just deploy a Windows Enterprise CA for creating your own test certificates.
I’m just starting to deploy Lync 2013. I’ve completed are the prereqs and completed the installation of the Lync server 2013 server FE. The problem I’m having is that the Lync Server services are not coming up. Any suggestions. Throughout the installation process all logs show a sucessfull installation.
With no deployment errors I can’t even begin to guess. I would start with whatever the server logs report when the services fail to start.
Hi Jeff
I currently have a Lync 2010 Enterprise Pool deployed and am attempting to deploy a segregated Lync 2013 Enterprise Pool for testing and development. The test servers are in the same domain as the production servers, but I have installed a separate SQL instance and file share. I have also created a test UPN, as I do not want to use current SIPs. I have just completed the Lync 2013 topology builder, but I am unable to publish, and am presented with an error stating that my original SQL instance was not defined in the topology.
My question is, is there a simple way to deploy two segregated Front End Pools in the same domain? I’d prefer to have two separate topologies and not to have to use the same SQL instance if I can get away with it. Any advise you can provide will be greatly appreciated.
Thanks,
Adam
Not sure there, as I never recommend mixing production and test/dev environments in the same AD forest and Lync topology.
Hi All,
Please some one let me know how to impot the certificate on all the front end server for the same pool.
We have 3 servers in same pool and i imported the certificate in first server and after that am unable to importthe same certificate on the next 2 front end servers.
Make sure that you are exporting the entire certificate, including the private key from, the server where the original request was generated. You cannot simply import the signed certificate file from your CA to all servers. you have to import that into the server with the original request to complete the certificate (public key + private key). Only then can you export the entire certificate to a file and then import that file into other servers.
Can we use OCS 2007 R2 , Lync 2010 & 2013 in same topology?
That is unsupported. Only two platforms in a single environment at one time.
Migration Lync 2010 to Skype for Business 2015 directly supported?
Not using the in-place upgrade method. You’ll have to stand up separate servers to migrate users from 2010 to 2015: https://technet.microsoft.com/en-us/library/Dn951396.aspx
Hey Jeff congrats for this fantastic post!
One question: this is the second part, where we installed RTCLOCAL and all Lync services. But what about the part 1? Do we need to go through Install or Update Lync Server System on the first server, where hosts the RTC ?
thanks
You need to go through each step sequentially until the green check mark appeared indicating that the step has been successfully completed.
You need to go through each step sequentially until the green check mark appears indicating that the step has been successfully completed.
Regarding the SAN UCUpdates-R2 and UCUpdates-R2.domain.com for the front end cert, are these required for Lync Phone Edition devices (CX600) as previously mentioned in your post?
http://blog.schertz.name/2013/05/updating-lync-phone-edition-devices-lync-2013/
Yes, but only if you need to support unregistered updates for LPE devices as explained in that article.
Hi Jeff,
Greetings!!!
I am getting error in power shell while running any cmdlet in lync 2013 edge server.
“Get-CsPool : Verify that Active Directory is prepared for Lync Server.
At line:1 char:1
+ Get-CsPool
+ ~~~~~~~~~~
+ CategoryInfo : NotSpecified: (:) [Get-CsPool], ADOperationExcep
tion
+ FullyQualifiedErrorId : Microsoft.Rtc.Management.ADConnect.ADOperationEx
ception,Microsoft.Rtc.Management.Xds.GetPoolCmdlet
Hi,
Received this error message in process pending certificates in skype for business server 2019
Retrieve pending certificates from the certification authority and add them to the certificate store.
Request-CSCertificate -Retrieve -Verbose -Report “C:\Users\Feserver\AppData\Local\Temp\Request-CSCertificate-[2018_07_04][18_07_57].html”
Creating new log file “C:\Users\Feserver\AppData\Local\Temp\Request-CSCertificate-[2018_07_04][18_07_57].xml”.
Create a certificate request based on Skype for Business Server configuration for this computer.
Issued thumbprint “” for use “Default,WebServicesInternal,WebServicesExternal” by “SFUA.Lync.com\ROOT-CA”.
Creating new log file “C:\Users\Feserver\AppData\Local\Temp\Request-CSCertificate-[2018_07_04][18_07_57].html”.
WARNING: Request-CSCertificate failed.
WARNING: Detailed results can be found at “C:\Users\Feserver\AppData\Local\Temp\Request-CSCertificate-[2018_07_04][18_07_57].html”.
Command execution failed: Value cannot be null.
Parameter name: thumbprint
Regards,
Navin