Now clearly the title of this article is a bit misleading as you cannot authenticate and sign-in to the Lync registrar using an Active Directory user account which is disabled. But the scenario often exists where a SIP client may need to register as a disabled account. For example the native registration of a Polycom HDX UC endpoint located in a conference room would often be tied to an existing Meeting Room mailbox defined in Exchange Server. But as Exchange Server resource mailboxes by default are AD-disabled user accounts then the credentials of that account cannot be used to register to Lync Server.
The easiest approach is to simply re-enable the user account and set a password on it. Although this account will still continue to function correctly Microsoft does not recommend those accounts to be re-enabled. A solution that requires more administrative effort is to just create a new AD account for every endpoint which needs to sign-in to Lync Server and just use separate accounts for Exchange and Lync on each endpoint.
An alternative approach is to create a single ‘master’ AD user account which will be used to authenticate to the Lync registrar on all endpoints yet the unique SIP URI of each disabled account (resource mailbox) will still be used. This one-to-many approach allows all endpoints to register as the unique meeting room account, yet a single set of credentials can be used.
The use case scenario shown in this article covers the configuration of a Polycom HDX 4000 UC endpoint to Exchange Server 2010 SP1 for Calendaring integration and Lync Server 2010 for SIP registration. Although this approach is not technically supported by Microsoft it does work in OCS and Lync 2010 environments.
In order to sign-in with the SIP URI of one account, yet pass the credentials of another account the primary account must first trust the secondary account to allow this. In Exchange the ‘master’ account is simply granted Full Access rights to the mailbox using either the Exchange server Management Console or Shell. In OCS/Lync Server the steps are a bit more complex and require manually editing the source account in ADSIedit.
Update (April 2014): Lync 2013 no longer allows this one-to-many configuration as when multiple users attempt to sign-in to a Lync 2013 registrar using the same AD account for authentication then connectivity to Lync web services will fail for the additional users, reporting the following error in the logs:
X-Ms-diagnostics: 28064;source=”<FE-FQDN>;reason=”Multiple users found in AD for given PUID/SID.”\
Lync 2013 will allow unique authentication accounts to be defined for each Lync account in a 1:1 fashion, which does not really accomplish anything. As Microsoft already supports enabling Exchange resource accounts for authentication on platforms like Lync Room System then using the same approach for other Lync clients and endpoints also works fine.
SIP Registration
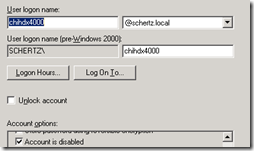
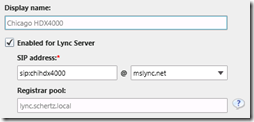
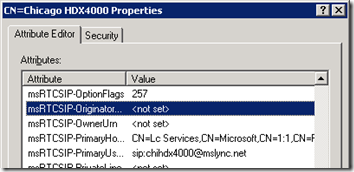
This scenario uses an existing disabled user account named "’Chicago HDX4000’ which is mailbox-enabled using the SMTP address of chihdx4000@mslync.net and is Lync-enabled with the SIP URI of chihdx4000@mslync.net. The exact same steps can be used on OCS 2007 and 2007 R2 deployments as well as Lync (which is the primary focus of this article).
Delegate Permissions
- Create a new ‘master’ user account in Active Directory (e.g. hdxsa@schertz.local). This account is used only for authentication and should not be enabled in either Exchange or Lync server.
-
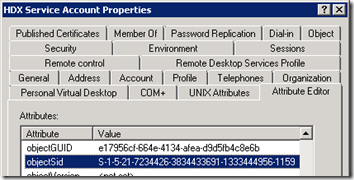
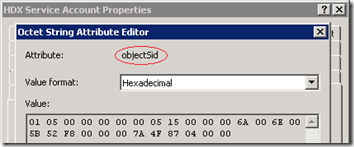
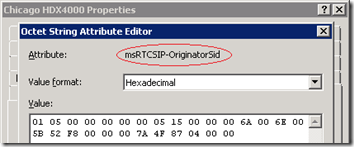
Using either ADSIedit or the Attributes tab in Active Directory Users and Computers locate the objectSid attribute on the new ‘master’ account.
- Edit the attribute and copy the contents of the hexadecimal data on to the clipboard.
- Still using ADSIedit or the Attributes tab find one of the existing user accounts configured as an Exchange resource mailbox (e.g. Chicago HDX4000) and the locate the msRTCSIP-OriginatorSid attribute on the disabled user account.
- Edit the attribute and paste in the copied string (which is the objectSid of the master account) into the msRTCSIP-OriginatorSid attribute. This will grant the master account the ability to authenticate to the Lync Server when the SIP URI of this account is used to sign-in.
Configure Endpoint
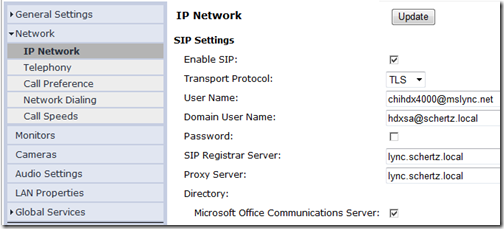
- On the HDX Admin Settings page browse to Network > IP Network and then Enable SIP. Select TLS as the Transport Protocol and enter the Lync Server/Pool FQDN (e.g. lync.schertz.local) in for both the Proxy Server and Directory.
- The User Name field should contain the SIP URI of the AD-disabled, Lync-enabled account.
- The Domain User Name should contain the Universal Principal Name (UPN) of the new master account.
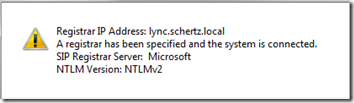
- From the Diagnostic menu on the HDX go to System Status and validate that the SIP Registrar Server status is shown as a green arrow. Click on the link to display the registration status, as see below.
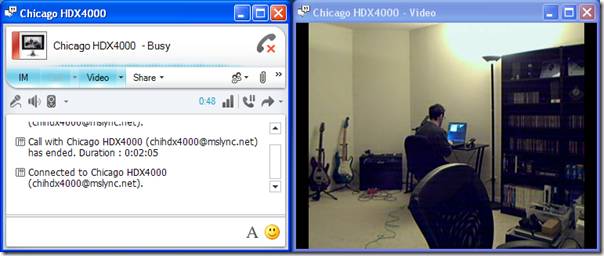
- Once registered, presence of the HDX can be seen and video calls placed directly to it from any Lync client. The screenshot below shows me placing a video call from a Lync client on a laptop to my HDX on the other side of the room which was configured for auto-answer.
Calendar Integration
These optional steps are for setting up the additional Calendar Service integration and not required for basic SIP registration.
Delegate Permissions
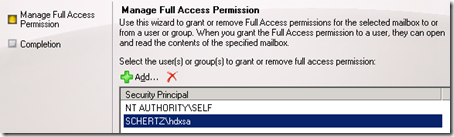
- Using the Exchange Server Management Console select the resource mailbox and then grant Full Access rights to the new ‘master’ user account (e.g. SCHERTZ\hdxsa).
- Alternatively use the Exchange Server Management Shell to issue the following cmdlet to perform the same procedure.
Add-MailboxPermission -Identity ‘CN=Chicago HDX4000,OU=Resource Mailboxes,OU=JDS,DC=schertz,DC=local’ -User ‘SCHERTZ\hdxsa’ -AccessRights ‘FullAccess’
Configure Endpoint
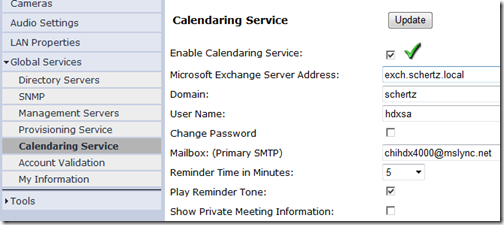
- On the HDX Admin Settings page browse to Global Services > Calendaring Service and then Enable Calendaring Service. Enter the FQDN of the Exchange Client Access Server in the Microsoft Exchange Server Address field (e.g. exch.schertz.local).
- The Domain field should contain the Active Directory NETBIOS domain name.
- The User Name field should contain the sAMAccountName of the new ‘master’ account.
- The Maibox field should contain the SMTP address of the AD-disabled, Exchange-enabled account.
[…] This post was mentioned on Twitter by Jeff Schertz, Jeff Schertz. Jeff Schertz said: Lync SIP Registration with Disabled Accounts http://bit.ly/e62hjz […]
[…] Lync SIP Registration with Disabled Accounts « Jeff Schertz’s Blog Posted on November 29, 2010 by johnacook http://blog.schertz.name/2010/11/lync-sip-registration-with-disabled-accounts/ […]
[…] Lync SIP Registration with Disabled Accounts « Jeff Schertz’s Blog Posted on December 13, 2010 by johnacook http://blog.schertz.name/2010/11/lync-sip-registration-with-disabled-accounts… […]
Hi Jeff,
after pasting the sidHistory into the msrtcsip-SidOriginator, it is displayed in the following formt /01/05/00/…
Does this look right?
Dave, the slashes should not be shown but it may depend on what tool you are using. If the Attribute Editor is used then it should look exactly like my screenshot.
Hi Dave – I got the same thing, but it worked just fine.
Hi Jeff – this is extremely useful info. We are struggling with this issue ourselves. I will be discussing this blog post with our AD and Exchange teams.
I would like to make a central forest topology. I 've created two accounts one in main forest and another in resource. The account in main is disabled. I copied the attribute :objectSid from resource account , and added it to the disabled account in main forest to msrtcsip-SidOriginator attribute. .The format of msrtcsip-SidOriginator is /01/05/00/… . When i try to log into resource forest account Lync doesn't work. It say's that it couldn't find server. What I made wrong? I can send You my snooper logging file.
Best regards,
Paul
Hi Jeff,
Can a mailbox for HDX4500 in Exchange 2007 be configure as Regular , Equipment or Room to be able to work?
You can use any type of Exchange mailbox role, just be aware that if resource accounts are used then you'll need to either re-enable the AD account or configure delegated account authentication.
Awesome post Jeff, clear and easy to read.. I see you have a picture on your resource too, does that account need to be enabled to allow replication of the picture then disabled again how did you get that picture to populate?
The photo is added to the Lync user account no differently than that other Lync accounts and should appear the same.
Hi Jeff
Great Post.
Room Resource Mailbox works fine.
Thanks
Can anyone help me to know do we require License for Rmx and HDX devices
You should contact your local Polycom reseller for these details. There are no licenses on the RMX specific to Lync interoperability, while the HDX does utilize a single Options Key for native Lync features.
Do we have any script to pull objectSID from the user forest and put it in the msRTCSIP-OriginatorSid attribute of the resouce forest.
Hi Jeff, we want to do something similar but simpler with room mailboxes. I've enabled some in Lync so our users can add them in their Lync contacts. They want to have them visible at a glance so when they get a call from a client which requires a few people in the conversation they can move into one if it doesn't already have a meeting booked. We tested this, but the problem is that the room in Lync just show their presence as "offline". Is it possible for these room mailbox users to just get their presence information from Exchange, so they will only show as "Available" or "In a Meeting"?
Presence updates from Exchange is not currently supported, it only comes from the actively registered SIP endpoint. But this is no different than the standard Lync architecture, as if I'm not signed into Lync somewhere then I will show offline regardless as to what my calendar might contain.
quick question, if I change that attribute then decide we want to remove the "master" account and enable the userid on the resource, will this cause any issues. Or can we simply just remove the attribute?
Curtis, you can simply null-out the [i]msRTCSIP-OriginatorSid[/i] attribute on the desired user to re-enable authentication for that account itself.
Have this setup and works fine somewhat, exhnage calendar is not updating often enough, and sometimes doesnt update at all with new events.
Actually just stopped updating.
Any suggestions to force phone grab calendar from exchange?
There is no way to change that behavior. Also if you are using Lync 2013 then this approach is no longer advisable (see the update near the top of the article).
This approach is no longer recommended with Lync 2013 (see the update at the top of the article).
Hello jeff, can you please give me alternate solution for this setup, i am using multiple users attempt to sign-in to a Lync 2013 registrar using the same AD account for authentication and its getting failed.
Please suggest
As I've mentioned in the article this is not possible in Lync 2013, you must create a separate dedicated authentication account for each Lync user account if you wish to not allow authentication on the primary account itself.
Jeff, i’m working with a new Trio 8800 and Office 365 for both Skype4B and Exchange. I’d like to set up account(s) to associate the device with a conference room that has it’s own SIP address and Calendar. What kind of accounts are needed, and what steps would you recommend? Can this be done with a Resource account, or will it require establishing the room as a ‘user’ (burning a license)?
You can use either a standard Lync account or mimic the LRS configuration I’ve covered in a previous article (see the LRS tag). Either approach is supported.
hello,jeff, could you please help me to set up my sip function on tri 8800? It shows that sip account is not registered. But this account works normally on my other sip phone.What should i do?
I can’t begin to guess what the problem could be. Suggest contacting your support channel or trying the Polycom Community support forums for assistance: https://community.polycom.com/t5/Skype-for-Business/bd-p/skypeforbusiness