This blog post is part 2 of a multi-article series and is a continuation of this previous article:
Lync Server 2010 Deployment – Part 1
Where Part 1 left off was just shy of deploying the Standard Edition server itself as most of the back-end configuration was completed. A few additional steps will be left for later discussion (e.g. client Automatic Configuration DNS records) when those topics are addressed. So for now left’s get the Lync Server deployed an functional.
Update: This process is identical to (and has been tested with) the public release version of Lync Server 2010.
Install Lync Server System
What these steps do is install a second SQL Express named instance (this one being named RTCLOCAL) on the local server which will contain a replica of the existing RTC named instance. Although it may initially seem inefficient to have two SQL instances with duplicate data on the same server the separation of the Central Management Store and a CMS replica is key to how multiple server’s function in a single organization.
Only the first Standard Edition server in the organization would contain this authoritative RTC instance, while all other Lync Front End Servers (and even Edge Servers) would contain their own RTCLOCAL instance to replicate the Central Management Store data. This approach also allows for the new redundancy and availability features which were lacking in previous versions of OCS. This RTCLOCAL instance can only ever be stored in an automatically installed SQL Express instance, it is not supported to locate this data in a full SQL Server instance.
- Back at the Deployment Wizard main menu select Install or Update Lync Server System. Run Step 1: Install Local Configuration Store and leave the default setting to Retrieve the configuration data directly from the Central Management Store. By reviewing the results in the execution window we can confirm a number of actions, most importantly that the second SQL Express instance of RTCLOCAL was installed.
<snipped>
Checking prerequisite PowerShell2…prerequisite satisfied.
Checking prerequisite SqlExpressRtcLocal…installing…success
Checking prerequisite VCredist…prerequisite satisfied.
Checking prerequisite SqlNativeClient…prerequisite satisfied.
Checking prerequisite SqlBackcompat…prerequisite satisfied.
Checking prerequisite UcmaRedist…prerequisite satisfied.
Installing OcsCore.msi(Feature_LocalMgmtStore)…success
- Secondly the Local Configuration Store was installed and enabled using the Import-CsConfiguration and Enable-CSReplica cmdlets.
> Install Local Configuration Store
Import-CSConfiguration -FileName "C:\Users\ADMINI~1.CSM\AppData\Local\Temp2\CSConfigData-2010_09_15-12_19_04.zip" -Verbose -LocalStore> Enable local replica service
Enable-CSReplica -Verbose -Confirm:$false -Report "C:\Users\administrator.CSMVP\AppData\Local\Temp2\Enable-CSReplica-[2010_09_15][12_10_23].html"
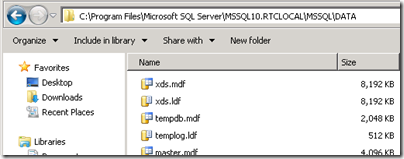
- To confirm the location of the RTCLOCAL database files on the server check the default SQL Server installation directory for the existence of the xds files.
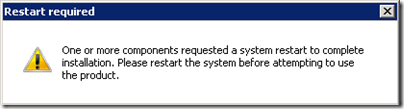
- Run Step 2: Setup or Remove Lync Server Components and if the process halts with an error requesting a reboot as shown below then restart the server and run this step again. This can occur because the Windows Media Format Runtime package requires a server restart after installation.
Checking prerequisite Wmf2008R2…installing…failure code 3010
The server must be restarted before installation can continue. To continue the installation after the server has restarted, start the Deployment Wizard and complete this step again.
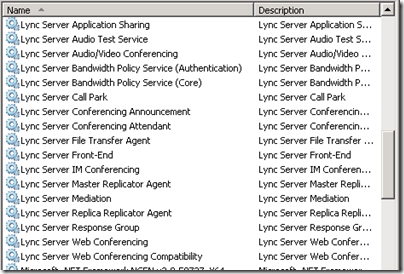
- At the completion of this step all of the Lync Server services and components have been installed locally. A look at the Services applet will show a large list of installed services which are not yet running as a certificate still needs to be configured and assigned to them.
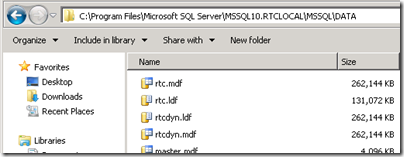
- Some of the newly added database files for the pool can be seen in the default SQL Server DATA directory as well.
So about now would be a good time to briefly sidebar and try to understand what is going on with all these different SQL instances and databases with similar names. I was scratching my head as well the first time I installed all this in an early beta release. So basically here is a brief rundown of
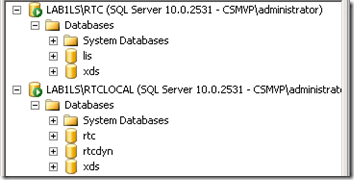
- Using SSMS there are two instances (both SQL Express) on the Lync Server, RTC and RTCLOCAL on the server to connect to, each with a different set of databases.
Instance Database Description RTC lis Location Information Services data RTC xds Central Management Store data RTCLOCAL rtc Standard Edition Pool data RTCLOCAL rtcdyn Standard Edition transient user data RTCLOCAL xds Local replica of Central Management Store data
And now moving back into the server deployment the next pending step is to request and assign a certificate so that the services can be started.
- Run Step 3: Request, Install or Assign Certificates and then expand the Default Certificate entry to verify that all roles are checked. Click Request and enter the information listed in the following tables.
Delayed or Immediate Requests
Send the request immediately to an online certificate authority
Choose a certificate Authority
Select from a list detected in your environment
(LAB1DC.csmvp.net\CSMVP-RootCA)
Certificate Authority Account
(skipped)
Specify Alternate Certificate Template
(skipped)
Name and Security Settings
Friendly Name Lync SE Certificate Bit Length 2048
Organization Information
Organization <Company Name> Organizational Unit <Department Name>
Geographical Information
Country/Region United States State/Province IL City/Locality Chicago
Subject Name / Subject Alternate Names
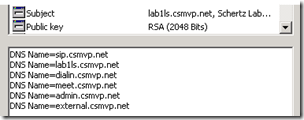
Subject Name lab1ls.csmvp.net Subject Alternate Name lab1ls.csmvp.net
dial.csmvp.net
meet.csmvp.net
admin.csmvp.net
external.csmvp.net
SIP Domain setting on Subject Alternate Names (SANs)
Configured SIP Domains csmvp.net
Configure Additional Subject Alternate Names
(skipped)
- This process will execute the Request-CsCertificate cmdlet with the provided configuration information, performing and online request against the CA and then automatically importing the return certificate into the Local Computer store.
> Request Certificate
Request-CSCertificate -New -Type Default,WebServicesInternal,WebServicesExternal -CA "LAB1DC.csmvp.net\CSMVP-RootCA" -Country US -State "IL" -City "Chicago" -FriendlyName "Lync SE Certificate" -KeySize 2048 -PrivateKeyExportable $False -Organization "Schertz Lab" -DomainName "sip.csmvp.net" -Verbose -Report "C:\Users\administrator.CSMVP\AppData\Local\Temp2\Request-CSCertificate-[2010_09_15][14_55_56].html"
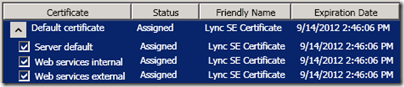
- Click Assign and select the new certificate from the local store. The following Set-CsCertificate cmdlet is automatically run by the wizard to assign the desired certificate to the three server roles.
> Assign Certificate
Set-CSCertificate -Type Default,WebServicesInternal,WebServicesExternal -Thumbprint 7B8E17E800F4702EC14228C4A6E84C019F9F6AB6 -Verbose -Confirm:$false -Report "C:\Users\administrator.CSMVP\AppData\Local\Temp2\Set-CSCertificate-[2010_09_15][15_03_04].html"
- Once the certificate is assigned to all roles the wizard should reflect that, although a Refresh may need to be required to see the changes.
- Run Step 4: Start Services to see the fruits of your labor converted into a bunch of happily-running services. The Start-CsWindowsService cmdlet is executed with no parameters which by default will attempt to start all Lync services.
> Start Services
Start-CSWindowsService -NoWait -Verbose -Report "C:\Users\administrator.CSMVP\AppData\Local\Temp2\Start-CSWindowsService-[2010_09_15][15_40_36].html"
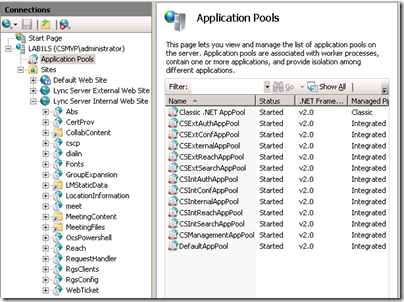
Let us briefly take a look at another major difference between OCS and Lync which is how IIS is configured by the installation process.
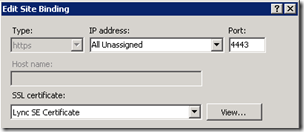
- For one, certificates previously had to be manually defined and SSL enabled in IIS, but in Lync Server the setup wizard now does this automatically.
- The other noticeable difference is the amount of new Application Pool defined, as well as the separate internal and external web sites.
Because there was no step in the deployment asking for additional IP addresses and it is still a best practice to use a single IP address on the Standard Edition server the External and Internal web sites in IIS are clearly not configured on the same listening ports.
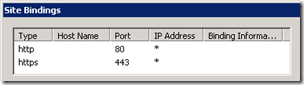
- The Lync Server Internal Web Site shows the default TCP80 and TCP443 ports assigned to it.
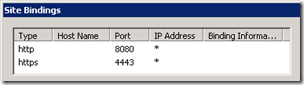
- Yet the Lync Server External Web Site indicates different listening ports of TCP8080 and TCP4443 ports. This configuration indicates that an external publishing server (e.g. ISA Server) must be configured to listen for client connections on the standard 80 and 443 ports yet it will forward traffic to the internal Front End server over ports 8080 and 4443 so that external client connections are directed to the External Web Site.
Before enabling user accounts now would be a good time to add the required internal DNS records to support Automatic Configuration. This is allow for any AD Integrated replication to fully propagate the new DNS records before attempting to sign-in with the Lync client.
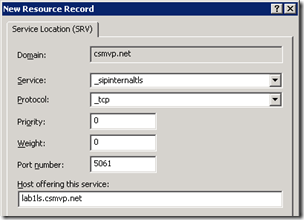
- Create a DNS Service Locator (SRV) and Host (A) records on the internal DNS server’s forward lookup zone.
As a general best practice I always prefer to add a second DNS record which the client will use as a fallback during Automatic Configuration in the case that the SRV record is not available or unsupported. The Communicator and Lync clients will automatically lookup sipinternal, sip, and sipexternal host records in the SIP domain if the SRV lookup first fails.
- A quick look at the details of the requested certificate shows an additional entry for sip.csmvp.net in the Subject Alternate Name field even though it was now specifically entered in the certificate wizard. The ‘Configured SIP Domain’ which was identified as csmvp.net during the setup automatically added a “sip.” record for that domain, so that record will suit our purposes.
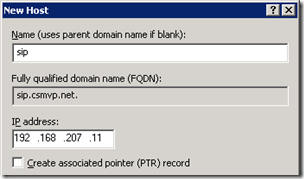
- Create a new DNS Host (A) record on the internal DNS server’s forward lookup zone for the desired SIP domain (e.g. sip.csmvp.net) and provide the same IP address which is statically assigned to the Lync Front End server.
- Verify the new records using the following nslookup commands from the standard Windows Command Prompt.
C:>nslookup -q=srv _sipinternaltls._tcp.csmvp.net
_sipinternaltls._tcp.csmvp.net SRV service location:
priority = 0
weight = 0
port = 5061
svr hostname = lab1ls.csmvp.net
lab1ls.csmvp.net internet address = 192.168.207.11C:>nslookup sip.csmvp.net
Name: sip.csmvp.net
Address: 192.168.207.11
Lync Control Panel
In a major shift away from MMC-based management consoles Lync Server can only be managed by either the Silverlight-based Lync Server Control Panel or the PowerShell-based Lync Server Management Shell.
- Launch the Lync Server Control Panel from the Microsoft Lync Server 2010 (RC) program group and re-enter the current account’s credentials. (Make sure this account has been added to the CsAdministrator domain group as covered in the Part 1 article.)
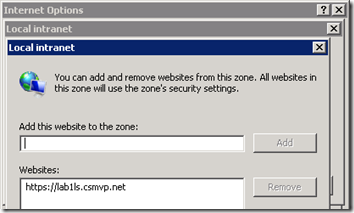
- (Optional Step) In order to suppress the additional authentication prompt when opening the control panel then on local server go to Internet Options > Security > Local Intranet > Sites > Advanced and add the FQDN of the Lync Server to the zone (e.g. https://lab1ls.csmvp.net).
At this point we should have a fully functional Lync Server and are ready to start configuring accounts, policies, and additional services. Part 3 in this series moves on to enable a few user accounts for Lync Server to test client connections to the Front End server.

Hi Jeff, eagerly awaiting Edge Server configuration! Have mine up and running and can IM, but voice calls are failing and somehow seem to be referencing an internal hostname, but I can't for the life of me figure out where that hostname is configured…
Am I right in understanding that every time you need to make a change, you have to load the topology file, adjust it, and then rerun the deployment wizard to initiate the changes?
[…] October 1, 2010 by Jeff Schertz · Leave a Comment This blog post is part 3 of a multi-article series and is a continuation of this previous article: Lync Server 2010 RC Deployment – Part 2 […]
Hi Jeff,
thanks for your perfect introducing.
I'am getting an issue In Step 2 "Setup or Remove Lync Server Components"
Error: Access control list (ACL) share failed.,Microsoft.Rtc.Management.Deployment.ActivateMachineCmdlet Access control list (ACL) share
I created the share manually like your introducing Part 1. After the Step "Publish Topology" was no error.
Maybe you can help me.
Regards
Sven, that is a pretty specific error and may be related to the domain account you are using to deploy Lync Server with. I'd suggest you post your question on the TechNet forums: http://social.technet.microsoft.com/Forums/en-US/…
Hi Jeff Schertz,
Please provide any information over the migration of OCS 2005 SP2 to Lync 2010.
We are planning for the implementaion in the current 2005 SP2 environment.
Also there are no proper info regarding this in MS websites.
Regards,
Manju
Manju,
Microsoft does not support a direct migration from LCS 2005 to Lync Server 2010. You would have to first migrate both clients and servers to either OCS 2007 or OCS 2007 R2, and then migrate again to Lync Server. See this TechNet article for more details: http://technet.microsoft.com/en-us/library/gg4257…
nice article, keep the posts coming
Thanks for good stuff
very informative blog thanks
Can you provide a breakdown of which certificates that have to be purchased for the Front End and Edge servers. I have a simple topology of 1 FE server and 1 consolidated Edge. I plan on buying from Entrust. Thanks in advance.
I'll ask in the Technet Forums instead, I see your most active there 😉 Nice blog entry on this though, thanks for the effort put into this.
The certificate configuration is basically the same as I covered in my OCS articles as the same Edge roles are still in place. There are new external FQDNs in Lync (e.g. meet, dialin) but those are part of the reverse proxy configuration and are not on the Edge Server. You still should follow the single cert for FE and multiple cert for Edge (private internal and AV auth with public Access Edge and Web Conf).
[…] lab environment used as examples was built using the same processes discussed in these three previous articles for Lync Server. A single consolidated Exchange 2010 SP1 server was also added with […]
[…] lab environment used as examples was built using the same processes discussed in these three previous articles for Lync Server. A single consolidated Exchange 2010 SP1 server was also added in […]
[…] The next article in this series jumps right into that process with Part 2. […]
[…] Part 2: http://blog.schertz.name/2010/09/lync2010rc-deployment-part2/ […]
[…] Part 2: http://blog.schertz.name/2010/09/lync2010rc-deployment-part2/ […]
hello,
Great article. Probably better than the official deployment guide. I could sucessfully deploy a standard edition lync server with remote access in a lab environment. everything except joining an online meeting worked fine initially. When i clicked on the "join the meeting" link , web browser returned an apllication error "meet"..I then checked IIS logs for further troubleshooting and realised that only anonymous authentication was enabled for the meet virtaul directory. (for both internal and external site). Is this some sort of a problem or by design implementation ? By the way the official standar edition deployment guide has a section for setting up a kerberos account for web services authentication. Do you have info about why we need this and if there is a correlation between the problem i had ?
Thanks and keep up the good work.
Ozgur, I'll have to take a look at that as well as more throughly test the conferencing functionality in the lab I've used to create this article. Is this issue only impacting externally joining clients (via Edge) or even internal users as well?
Hi Jeff,
I wanted to request a cert from external CA and this is what I have done so far.
– The first topology had some URL issues so I created another topology that included changed URLs including the Admin URL. When I proceed with requesting a cert (offline) it still shows me the old URLs (incl admin URL)
I have already published the new topology.
Do I need to delete the old topology and then publish the new one.
This server will be accessed by the clients within our domain network and there is only one SE server. Yes, its a business decision to go with public CA rather than internal CA. Our AD domain is public FQDN.
Any help would be much appreciated
I have a problem using a public (GlobalSign) certificate on the Frond End server.
We want to do this so that external users can use our CS while the are inside our office.
The wizard does not show the public certificate, even with the intermediate certificate already imported.
In the windows certificate manager the certificate show's as OK, but when i assign it using powershell (because the wizard does not work), logging shows "The chain of the certificate XXXXXXXXXXXXXXXXXXX is invalid".
Altough everything seems to work, it does not seems right.
Anyone with a solotion?
Your Lync Edge server requires the "special" intermediate certificates from GlobalSign used for Exchange and OCS (http://www.globalsign.com/support/intermediate-root-install.php). Then it will show up in wizard.
Hi Jeff – many thanks for your personal contributions to the UC world – have followed many of your articles for deployment (OCS and now Lync). I'm having trouble after enabling my Lync edge server. The problem is with users that are still on 2007R2 that try to connect to the LiveMeeting/WebConf services on the OCS pool through the Lync edge. I keep getting errors on the Lync edge regarding 'the web conferencing server that's trying to connect isn't in the internal servers list'. I don't see a good way to add that server like you were able to on OCS Edge (just go add the server to the allowed or authorized hosts list). Is there a magic shell command to add the FQDN of my single-server OCS pool to the Lync edge trusted list?
Jay, thanks for the comments. Although I believe that information should automatically be pulled from the Topology you can verify it by checking the BackCompatSite details. <a href="http:// (http://technet.microsoft.com/en-us/library/gg412861.aspx)” target=”_blank”> <a href="http://(http://technet.microsoft.com/en-us/library/gg412861.aspx)” target=”_blank”>(http://technet.microsoft.com/en-us/library/gg412861.aspx) Did you merge the topology during Lync deployment?
Hey Jeff really good stuff. We just got Lync up and running, and we have OCS 2007R2. We would like to migrate the users, but we want to use a different SIP domain. We're afraid that the migration, because of the new SIP domain, will cause the existing users to lose their contacts and groups. Any thoughts on this?
One possible approach would be to merge the topology between OCS and Lync yet still use the new SIP domain in Lync. Then move users from OCS to Lync retaining their configuration and SIP URI. Once they are in Lync you can change the SIP URI to utilize the new SIP domain either through LSCP or PowerShell, depending on how many users are in the environment.
[…] Also make sure to verify that the Lync Server environment is correctly configured for Automatic Configuration of Lync clients. At minimum this includes creating a _sipinternaltls SRV record as discussed in this previous article. […]
Hi Jeff – I am trying to get my Lync server up and running but when I run the 'Setup Lyn Server Components, I get the following error:
Prerequisite not satisfied: The following IIS Role services must be installed before attempting to install this product: Static Content, Defaul Documentation, HTTP Errors, ASP.NET, .NET Extensibility, Internet Server API (ISAPI) Extensions, ISAPI Filters, HTTP Logging, Logging Tools, Tracing, Client Certificate Mapping Authentication, Windows Authentication, Request FIltering, Static Content Compression, IIS Management Console, IIS Management Scripts and Tools.
hello sir,
Error returned while Installing Webcomponents.msi( Feature_WebComponents_CommonFiles), Code 1603.
i m getting this error. it have been two weeks already. pls help me.
thanks
tinmyint ( tinmyint@hotmail.com)
[…] Part 2: http://blog.schertz.name/2010/09/lync2010rc-deployment-part2/ […]
[…] http://blog.schertz.name/2010/09/lync2010rc-deployment-part2/ […]
Hello Jeff,
thanks for your wonderful article, I have deployed lync 2010 and my domain is corp.abc.com and my users are using user@abc.com as an email address. I setup lync with corp.abc.com and when I was trying to enable users with their email address I had no success, however I want my users use their email address to sing in, Do I have to add additional SIP domain (abc.com) to make this work ?
You'll need to add a secondary SIP domain in the Lync Topology for the abc.com domain. You (typically) do not want to use your internal AD namespace as your SIP domain. Ideally the SIP domain should match your SMTP domain.
Thanks Jeff, Do I have to make changes to my DNS records and obviously I have to request a new certificate right ?
Appreciate for your help in advance.
Yes.
I added ABC.com in internal, but most of the stuff is not working because they are looking at the internal DNS and there is nothing in there. I ended up with removing the ABC.com zone.
Any suggestion?
Thank you,
You can' just add or change the SIP domain without first making sure that DNS zones and records are configured exactly as required. I suggest you revisit the original deployment design and make sure that you have all of the required records and the proper DNS configuration, and then you need to make all the changes (don't forget certificates) at the same time.
i has deployed lync 2010 standar runing in hyper-v over windows 10 enterprise 64 bits, guest is windows server 2008 r2 64 bits, all lyn client can log in excep for those running windows 10 64 and 32 bits version of SO. lync show up can not login because the server is temporaly unavaible. firewall is off in both the guest and host. all windows 10 cliente has firewall off. update client to version 4.0.7577.4488 but not luck also update de server to the latest cumulative update from 2015 and got the same result. any ideas how to solve this.