This edition in a series of deployment articles for Skype for Business Server 2015 addresses the integration of an existing Exchange Server 2013 installation with a recently installed Skype for Business Standard Edition server. The article outlines establishing the prerequisite partnership between each platform, allowing the Skype for Business server to leverage the Exchange Server database engine for storage of some types of data
Further configuration of additional features provided by this integration will be covered in later articles, as in Unified Contact Store, Exchange Unified Messaging, and Outlook Web App with Skype for Business Server 2015. For each of these additional integrations the following Partner Application relationship must first be enabled in the environment. An updated listing of only the articles specific to Exchange Server integration with Skype for Business Server 2015 can be found using this link
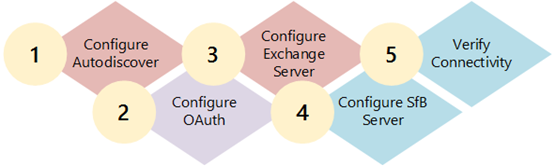
The sections in this article are outlined in the following configuration steps:
Configure Autodiscover
In the event that Exchange Autodiscover is not correctly configured this could prevent the Skype for Business server and clients from being able to locate the Exchange server and thus cripple the ability to complete this integration. The steps in this first section are optional and may not be required in all environments, so long as Autodiscover is correctly deployed.
In event that the existing autodiscover URL will be used then skip to the next section to configure OAuth.
Validate Configuration
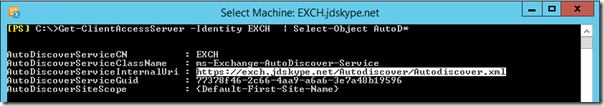
- Using the Exchange Server Management Console run the following Get-ClientAccessServer cmdlet to view the current Autodiscover configuration. The Identity parameter cab be either the Exchange server’s hostname or the Fully Qualified Domain Name (FQDN).
Get-ClientAccessServer -Identity EXCH | Select-Object AutoD*
In this example environment the default configuration is still applied whereas the server name is utilized in the internal autodiscover URL. This will be updated to use the well-known autodiscover record format which is generally an Exchange Server deployment best practice.
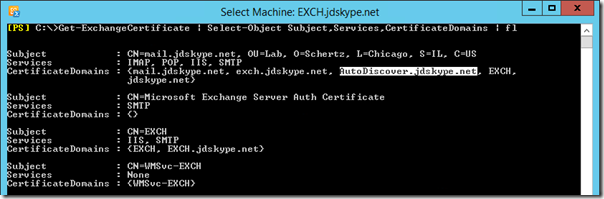
Most likely when the Exchange Server was originally deployed the Autodiscover option was selected which would have included the proper FQDN in the certificate request. To validate this the following commands can be used to identify and parse the server certificate currently assigned to Exchange Server roles.
- Using the Exchange Server Management Console run the following Get-ExchangeCertificate.
Get-ExchangeCertificate | Select-Object Subject,Services,CertificateDomains | fl
As seen in the example above the desired certificate should be the entry with a FQDN in the Subject which is also assigned to at least the IIS service. This example snows that the Subject Alternative Name (SAN) field of the certificate in use by IIS already includes the desired FQDN of autodiscover.jdskype.net.
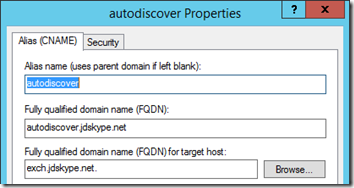
Create DNS Records
If the following two DNS records do not already exist in the environment then they need to be created before modifying the Exchange configuration. These are the two well-known DNS records that mostly autodiscover-aware clients will query when attempting to locate an Exchange Server.
- Create a new Alias (CNAME) record in the proper SMTP/SIP namespace forward lookup zone, pointing to the Exchange Server FQDN.
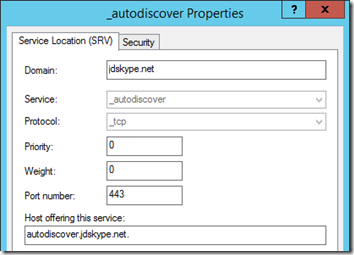
- Create a new Service Location (SRV) record using the following parameters, pointing this record to the CNAME record created in the previous step.
To validate the records were created successfully and are functional run the following two test commands from a command shell.
nslookup -q=srv _autodiscover._tcp.jdskype.net
_autodiscover._tcp.jdskype.net SRV service location:
priority = 0
weight = 0
port = 443
svr hostname = autodiscover.jdskype.net
nslookup autodiscover.jdskype.net
Name: exch.jdskype.net
Address: 192.168.0.101
Aliases: autodiscover.jdskype.net
Update Autodiscover URL
- Using the Exchange Server Management Console run the following set-ClientAccessServer cmdlet to update the configuration to use the new FQDN. The Identity parameter should be the Exchange server FQDN, while the new Autodiscover FQDN replaces the server FQDN in the internal URL.
Set-ClientAccessServer -Identity EXCH -AutoDiscoverServiceInternalUri "https://autodiscover.jdskype.net/autodiscover/autodiscover.xml"
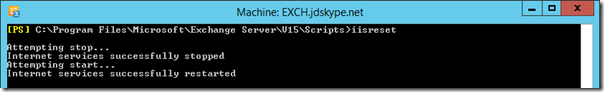
- When the process completes perform a reset of Internet Information Server to immediately apply the change using the following iisreset shell command. (If performing this in a production environment with active connections then it is recommended to use the /noforce switch.)
iisreset
Attempting stop…
Internet services successfully stopped
Attempting start…
Internet services successfully restarted
Configure OAuth
The Partner Application pairing provides the ability for the Skype for Business and Exchange servers to communicate with each other via an authenticated secure connection that does not require any third party system to negotiate or establish the session.
OAuth is the server-to-server authentication mechanism used between the Skype for Business and Exchange servers to establish secure communications. During the initial SfB server deployment in this article an SSL certificate was created specifically for OAuth.
Before defining Exchange Server as a partner application Skype for Business needs to know about the Exchange Autodiscover configuration.
- Using the Exchange Server Management Console run the following Get-ClientAccessServer cmdlet to query the existing internal autodiscover URL. This is either the existing or newly defined value, depending on whether the previous section was skipped or not.
Get-ClientAccessServer -Identity EXCH | Select-Object AutoDiscoverServiceI*
AutoDiscoverServiceInternalUri
——————————
https://autodiscover.jdskype.net/autodiscover/autodiscover.xml
Pay special attention to the fact that the retrieved autodiscover URL points to an .xml file; this will be important in a few steps.
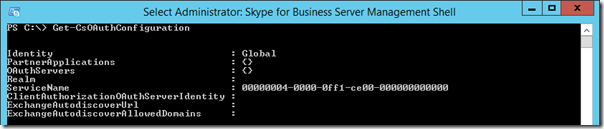
- On the SfB server open the Skype for Business Server Management Shell and enter the following Get-CsOAuthConfiguration cmdlet.
Get-CsOAuthConfiguration
The ExchangeAutodiscoverUrl parameter should be blank as it has not yet been defined.
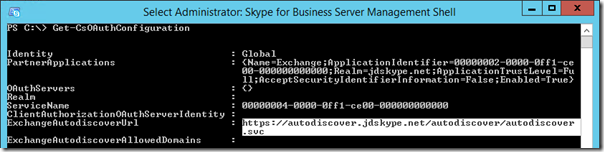
- Enter the following Set-CsOAuthConfiguration cmdlet to define the Exchange autodiscover location as shown below.
Set-CsOAuthConfiguration -Identity global -ExchangeAutodiscoverUrl https://autodiscover.jdskype.net/autodiscover/autodiscover.svc
In contrast to what was pointed out earlier the path provided above must end with .svc and not .xml. This is a minor detail not specifically called out in the TechNet documentation but can easily be missed, especially if cutting and pasting these strings between steps.
- Run the Get-CsOAuthConfiguration cmdlet again to verify the new parameter value is applied as intended.
Get-CsOAuthConfiguration
Configure Exchange Server
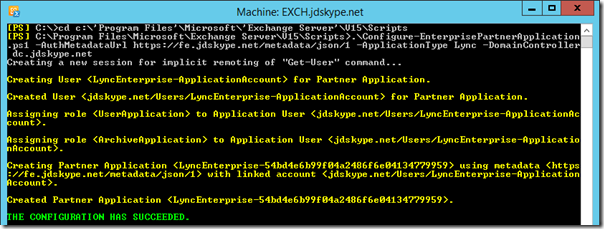
Enabling the partner application relationship requires that some configuration is performed on both side. Starting with the Exchange Server configuration pre-packaged script will be called while passing a few parameters. Before executing the script
- Identify the proper path for the Skype for Business server authentication metadata document. This URL should be identical to the following format, utilizing the SfB Front End server FQDN.
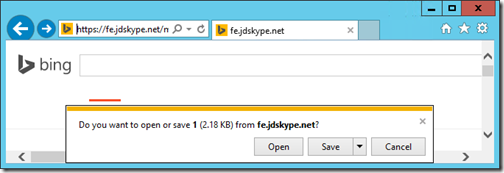
https://fe.jdskype.net/metadata/json/1
- Connect to this URL in a web browser from the Exchange Server to validate connectivity which should result in a prompt to open or save a file simply named ‘1’.
- Open the file using Notepad to view the contents, which should start with a x509 certificate string and end with the OAuth realm.
{"issuer":"00000004-0000-0ff1-ce00-000000000000@jdskype.net","keys":[{"keyValue":{"type":"x509Certificate","value":"MIIF2TCCBMGgA…
…xSTGd1KHw=="},"usage":"signing"}],"realm":"jdskype.net","serviceName":"00000004-0000-0ff1-ce00-000000000000"}
- Open the Exchange Server Management Console on the Exchange Server and change to the Scripts directory by using the following command.
cd c:\’Program Files’\Microsoft\’Exchange Server’\V15\Scripts
- Then execute the Configure-EnterprisePartnerApplication.ps1 script using the following command.
.\Configure-EnterprisePartnerApplication.ps1 -AuthMetaDataUrl ‘https://fe.jdskype.net/metadata/json/1′ -ApplicationType Lync"
- To complete the changes restart Internet Information Services using the iisreset command.
iisreset
Configure Skype for Business Server
To complete the pairing a new partner application will also need to be defined on the Skype for Business side.
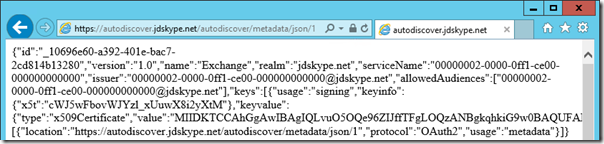
- Identify the proper path for the Exchange server authentication metadata document. This URL should be identical to the following format, utilizing the SfB Front End server FQDN.
https://autodiscover.jdskype.net/autodiscover/metadata/json/1
- Connect to this URL in a web browser from the Skype for Business Server to validate connectivity, which should look similar to the results the previous section.
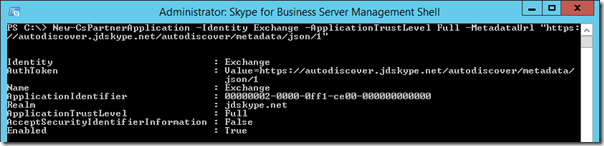
- Using the Skype for Server Business Management Shell enter the following New-CsPartnerApplication cmdlet to define the other half of the association.
New-CsPartnerApplication -Identity Exchange -ApplicationTrustLevel Full -MetadataUrl "https://autodiscover.jdskype.net/autodiscover/metadata/json/1"
Verify Connectivity
To validate that the partner application relationship has been successfully established a simple cmdlet can be run from the SfB Server.
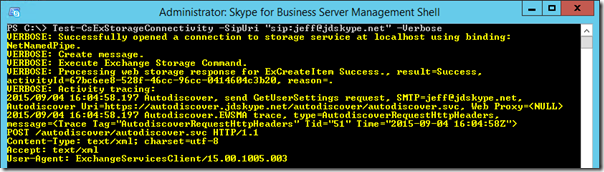
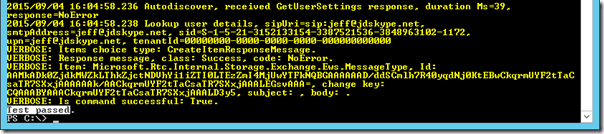
- Enter the following Test-CsExStorageConnectivity cmdlet, providing the SIP address of a user account which has already been enabled for Skype for Business. (The -Verbose parameter is optional and is used here to display additional information about the test process.)
Test-CsExStorageConnectivity -SipUri "sip:jeff@jdskype.net" -Verbose
If the test cmdlet fails to return a successful result of “Test Passed” then here are a couple of the most common issues.
- In the event that the Skype for Business OAuth configuration was previously defined with an incorrect ExchangeAutodiscoverUrl parameter, as could happen by accidentally using .xml instead .svc for example, then the following error may occur. In fact if this parameter is null or invalid in any way then this error can occur.
Test-CsExStorageConnectivity : ExCreateItem exchange operation failed, code=50043,
To resolve the above error define the proper ExchangeAutodiscoverUrl in Skype for Business server using the Set-CsOAuthConfiguration cmdlet as outlined earlier in this article.
- If the AD user account which is used to execute the test cmdlet does not have the correct permissions then the process will fail with the following error being reported.
Test-CsExStorageConnectivity : ExCreateItem exchange operation failed, code=5,
To resolve this issue follow the directions outlined in this TechNet article to add the account to the RTCUniversalUserAdmins universal security group.
Now that Exchange Server has been successfully integrated with Skype for Business Server then additional features can now be deployed. An updated list of articles covering other Exchange Server integration options can be found here.
Great series. Would you be so kind to outline what features are available and which are missing if using Exchange 2010.
You can find those features listed here: https://technet.microsoft.com/en-us/library/jj205269(v=ocs.15).aspx
Hi Jeff,
Great blog! Recently discovered it as we are establishing a new Skype for Business with Polycom handsets environment and I’m finding some great material here.
One thing I’m trying to find out is I have two users who jobshare a desk with a VVX500. They find the having to enter email, domain and password credentials each time the switch a reasonable overhead. Is there a smarter way to simplify this that you know of?
Kind regards,
Andrew
Not currently as only a single user account is supported. When Hotdesking support is added to the VVX then one user will be able to sign-in over the other when needed.
We have just deployed a number of LRS systems. One system and only one system will not accept meeting requests unless it initiates the request first. This is the same for lync meetings booked on outlook calendars or if we use the “meet now’ from the console. Any idea what we should look at to try to resolve this issue? The csmeetingroom info is the same for this room as our other rooms. The exchange client looks the same.
Ideas?
I would try deleting the LRS account and re-provisioning it with a new account, something may have gone wrong with the initial account configuration.
This is another great post, thanks Jeff.
Quick question, Have written any instruction on Skype for business (on-prem) with Exchange (online) you can point me to or a summary differences in configuration between the two (exchange online or on-premises and S4B on prem.)?
Thanks Jeff
If Directory Sync is being used in the environment and the user’s credentials are identical for both the on-premises SfB and Exchange Online servers then just use the UPN as the username (not DOMAIN\username) and that should work. I have not tested this scenario myself yet though.
Hi Jeff and thanks for great post. We have Exchange online and Lync server 2013. With this setup it worked fine, we just had to add CShostedprovider to Exchange online. It have been working fine until we did in place upgrade to SFB. Now Test-CsExStorageConnectivity fails for users in Exchange Online, but for users with mailbox On-Prem it works fine. I have removed everything and created it from scratch , but still it only works for On Prem mailboxes.
We had a case with Microsoft, but they say it is nothing they can do and we have to contact Exchange Online support.
Contacted them and they threw us back to Skype support.
I have therefor given up Microsoft support and have to find a way to fix it. All test according to your guide works fine (can browse both autodiscover and FE pool svc).
When we run Test-csexstorageconnectivity for Exchange online mailboxes it fails with 50043.
Does Skype for Business require another Autodiscover ?
thanks!
I’m not aware of this issue but MS support should not be bouncing you back and forth between groups. I suggest that you push back on them for a resolution. If it’s only the test cmdlet that does not work but the actual user functionality is there then I would not worry about it. I’ve seen scenarios where only the test cmdlets do not function as designed.
I’m having the same issue with Exchange online and SfB on Premise. Did you find a solution?
Thanks
Actually, I know what this is.
See when you run Test-csexstorageconnectivity, you use the OAUTH connection. What you need to do, is take your oauth certificate in your lync on-prem server, Export it into Exchange online and tada it should work. As long as you have your on-prem and you online setup to work together.
This is also the same process you use to make outlook.office365.com’s web lync sign in actually function.
The process is similar to this
https://support.microsoft.com/en-us/kb/2614242
and this
https://technet.microsoft.com/en-us/library/dn594521(v=exchg.150).aspx
Hi Jeff,
I’ve been searching all over for information regarding the 2016 Client and GAL searching.
I’m building a POC for a 2010 Exchange and 2015 Skype for business server and while I can manually add approved Skype users in my environment, I cannot “discover them” by going to add users. I only get my local outlook contacts.
What’s the easiest route to getting pre-populated AD users in my Skype client? Is there a way to do it without exchange integration or is that the only way to do it?
There are some third party tools out there to do this but I’ve never used them.
This is another great post, thanks Jeff.
I was trying to configure the step “Configure Skype for Bussiness Server”, and I can validate connectivity in a SFB Wer Browser, but the IE get Certificate Invalid… and I click on “Continue to this Web Site (note recommended)” and the results is similar the previous section.
when I tried to create an New-CsPartnerApplication, it got this error:
PS C:\Users\Administrator.TECNOPUTER> New-CsPartnerApplication -Identity Exchange -ApplicationTrustLevel Full -MetadataUrl “https://autodiscover.tecnoputer.com.br/autodiscover/metadata/json/1”
New-CsPartnerApplication : Cannot bind parameter ‘MetadataUrl’ to the target.
Exception setting “MetadataUrl”: “The metadata document could not be
downloaded from the URL in the MetadataUrl parameter or downloaded data is not
a valid metadata document, error: The underlying connection was closed: Could
not establish trust relationship for the SSL/TLS secure channel.”
At line:1 char:86
+ … l -MetadataUrl
“https://autodiscover.tecnoputer.com.br/autodiscover/metadata/jso …
+
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : WriteError: (:) [New-CsPartnerApplication], Para
meterBindingException
+ FullyQualifiedErrorId : ParameterBindingFailed,Microsoft.Rtc.Management.
Internal.NewPartnerApplicationCmdlet
Do you know how to fix that?
Rgds,
Ricardo.
I have the same issue. How did you fix it ?
Did you check whether
(Get-ExchangeCertificate).Thumbprint -contains (Get-AuthConfig).CurrentCertificateThumbprint
is true?
if it is false, you need to recreate the Auth Certificate on the Exchange server:
https://blogs.technet.microsoft.com/jenstr/2012/11/22/getting-internal-server-error-500-when-creating-new-cspartnerapplication-for-exchange-2013/
Were you able to fix this ?
I have the same issue – get certificate warning that it’s not trusted when trying to browse exchange metadata from Lync server .
The autodiscover is correctly setup in exchange and all exchange Certs and Lync certs are correctly setup .
what could be the issue ?? Pulling my hairs out on this ……any thought ms? Thanks in advance
Imported Ex cert into Lync server and it worked
Hi Jeff,
love reading your posts. It helped me a lot in past.
I have one problem and I cannot figure out what the issue is.
I have Exchange 2016 Lync 2013 environment and I have issue with SfB 2016 Client. I cannot establish MAPI connection with 2016 client and 2015 works without any flaws. I was wondering if you could get any pointers where I should be looking.
Thanks
Milan
I’m not aware of any differences in the clients that would cause this issue. I would suggest searching through the TechNet forums to see if anyone else has seen this.
Great post thanks.
We have Exchange 2013 and Lync 2013.
The integration works fine.
We are now upgrading to Skype for Business 2015 (using a new pool, not inplace upgrade).
However what do I do with the Exchange 2013 servers?
In the Skype topology I can move them to the new pool.
But what do I run on these Exchange 2013 (we have 5) servers?
Great post Jeff..Thanks a lot
Hi Jeff – you information has been invaluable to us.
We’re stuck at the exchange script:
.\Configure-EnterprisePartnerApplication.ps1 -AuthMetaDataUrl ‘https://fe.jdskype.net/metadata/json/1′ -ApplicationType Lync”
is that trailing quote correct? we’ve tried it both ways and also added the -domaincontroller parameter (shown in the image) as well, we just end up with a:
>>
sorted! just entered .\Configure-EnterprisePartnerApplication.ps1 without parameters and filled in prompts – working fine
Hi Jeff,
Very well explained
Just FYI…there is something wrong in the command because I also encountered and was stuck as “John Murray” post entered .\Configure-EnterprisePartnerApplication.ps1 without parameters and filled in prompts – worked fine me as well.
Many thanks,
Great article Jeff. Really helpful.
We are having an issue that nobody seems to understand how to correct. We are using a telco hosted Lync 2010 server with Lync 2013 clients. We are in the process of upgrading to Office 365 and installed Skype for Business using the Lync completeuc.com credentials to get phone presence. We are unable to see in call or meeting presence on any of the new users migrated over to the Skype for Business client however have a few that are still working correctly. We deleted all the old SIP profiles and did not solve the issue. Have you seen this before and does anything come to mind?
One thing that’s not obvious (to me) is that when the script is run on the Exchange server, it shows entering the FQDN of “the” front end server. Does it matter if we have multiple FE servers? Or even multiple pools? Do I run the command for each FE server? Or is adding one of the FE servers just a starting point for the script to load everything it needs?
Also, does this script need to be run on each Exchange server? Or do I just need to run it once for the environment? If I run it once do I need to do the iisreset on each Exchange server?
Thanks for the great information.
It only needs to be performed once per integration, not per server.
Dear Jeff Schertz
thank you very much for your training . Im mohamad From iran And test your Step. I get at the end of test “” Test Passed”” & now im very happy .with the best wishes for you And we are waiting for your next training.
Good luck
mohamad
Hey Jeff,
Redid my enviorment upon trying to integrate skype for biz with exchange 2013.
when I try to go to my front end
l”https://lrs-s4bfe.domain.com/metadata/json/1″ -ApplicationType Lync
I get a cert error when I go to it in a browser it does download “1”
Cannot acquire auth metadata document from ‘https://lrs-s4bfe.domain.com/metadata/json/1’. Error: The
underlying connection was closed: Could not establish trust relationship for the SSL/TLS secure channel..
cert issue?
Hey Jeff,
Great article. We are deploying Exchange 2016, and we are looking at Skype For Business online and sharepoint online. Is there any way to integrate this that you are aware of? From what I have been able to find it appears we can’t integrate S4B online (365) with on prem exchange 2016. Is this correct? any work around to make it work?
Thanks
Hi Jeff,
Was there a purpose why Lync FE FQDN and realm was written with the same colour even they were not the same? How these things are actually working, if you have multiple SIP domains?
This is another great post, thanks Jeff.
I was trying to configure the step “Configure Skype for Bussiness Server”, and I can validate connectivity in a SFB Wer Browser, but the IE get Certificate Invalid… and I click on “Continue to this Web Site (note recommended)” and the results is similar the previous section.
when I tried to create an New-CsPartnerApplication, it got this error:
PS C:\Users\Administrator.TECNOPUTER> New-CsPartnerApplication -Identity Exchange -ApplicationTrustLevel Full -MetadataUrl “https://autodiscover.tecnoputer.com.br/autodiscover/metadata/json/1”
New-CsPartnerApplication : Cannot bind parameter ‘MetadataUrl’ to the target.
Exception setting “MetadataUrl”: “The metadata document could not be
downloaded from the URL in the MetadataUrl parameter or downloaded data is not
a valid metadata document, error: The underlying connection was closed: Could
not establish trust relationship for the SSL/TLS secure channel.”
At line:1 char:86
+ … l -MetadataUrl
“https://autodiscover.tecnoputer.com.br/autodiscover/metadata/jso …
+
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : WriteError: (:) [New-CsPartnerApplication], Para
meterBindingException
+ FullyQualifiedErrorId : ParameterBindingFailed,Microsoft.Rtc.Management.
Internal.NewPartnerApplicationCmdlet
Do you know how to fix that?
Pleeeeeeeeeeeease Answer
Jeff great post. I am having some issues at this point. I get all the way through to the test of the Test-CsExStorageConnectivity -SipUri “sip:jeff@jdskype.net” -Verbose and it fails. The error says the certificate has validation failed.
My environment is as follows
Skype 2015 for Business with latest updates (standard with cert issues from local CA)
Exchange 2016 with latest update (self signed cert)
Should I be able to integrate with these?
Event ID I get is 32054
Yes it should work. I have had scenarios where the test cmdlets simply will not work yet the actual connectivity and functionality is fine so sometimes those errors can be a red herring.
I cannot access https://Pool FQDN/metadata/jaon/1 on either SFB server or the Exchange server, it returns HTTP 404 not found. Would you pls help?
Hi,
I’m trying to execute the new-cspartnerapplication and get an error that it cannot bind metadataurl. I think that the issue come from the fact that i’m using the self signed exchange certificate. Am i supposed to get a trusted certificate when i open the url autodiscover.mydomain.com/… ?
Right now i only have the three defaul certificate and nothing with the autodiscover url.
Thanks for your help.
Yes you must use a server certificate issued by a jointly trusted CA to allow SfB and Exchange to communicate via TLS, self-signed certificates are not valid for this integration.
Hi, I assume the process is the same for connecting to Exchange 2010. Are the commands in this guide valid for that, or can you point me to a resource for integrating Exchange 2010 and SfB 2015? I realized some features will not be present.
Thanks
Dan, the process for Exchange 2010 is slightly different due to changes on the Exchange side more than on the Lync/SfB side. I’d suggest using both of my articles together, side-by-side, to achieve this. I have not attempted it and haven’t even looked to see if it is supported either. There would only be a few differences at most though.
@Dan,
We you able to successfully integrate Exchange 2010 and SfB Server 2015?
I am in a similar situation, and struggling, because I still cannot make SfB Clients discover properly the Exchange 2010 EWS URLs and settings, and therefore do not display any info contained in Outlook calendar in the SfB client meeting/calendar tab.
Just to update, we sorted out the problem and were able to integrate SfB Server 2015 with Exchange 2010. It was all due to DNS and DNS entries. After addressing the issues with DNS the integration between both products works like a charm.
Hi,
I am in the process of migrating exchange 2013 to 2016 and they are now in coexistence. All traffic and settings are on the Exchange 2013.
But the users that has been moved to 2016 databases get the message when calling their um voicemail that the mailbox is not supported. It works fine for those who are still on exchange 2013 databases.
Must i set up partnerapplication between exch 2016 and skype server as well, can skype have multiple partner applications towards different exchange servers?
Hello,
I followed your procedure in full, but I have this problem that prevents the smooth operation:
Storage Service had an EWS Autodiscovery failure.
StoreWebException: code = ErrorEwsAutodiscover, reason = GetUserSettings failed, smtpAddress=christophe.dos@akdn.org, Autodiscover Uri = https: //autodiscover.aiglemont.org/autodiscover/autodiscover.svc, WebProxy Autodiscover = , WebExceptionStatus = TrustFailure —> System.Net.WebException: The underlying connection was closed: Could not establish trust relationship for the SSL / TLS secure channel. —>
I have checked and repeated your procedure several times, but it persists.
For information, SMTP addresses and SIP addresses are different.
For example:
User A:
SMTP Address: UserA@smtp.com
SIP Address: UserA@sip.com
Autodiscover URL: https://autodiscover.smtp.com/autodiscover/autodiscover.xml
Can you help me, or explain how it works with these different addresses?
Thank you
Olivier
Hi Jeff,
Partner Application is configured just fine.
The test works for multiple users in multiple sip domains, but one user in one sip domain does always fail.
Other users in the same sip domain are working fine!
Test-CsExStorageConnectivity : Fehler beim Exchange-Vorgang ‘ExCreateItem’,
Code=50043, Ursache=#CTX#{ctx:{traceId:18446744071570084743,
activityId:”d82e1825-ab54-4b09-bacc-f349e309c7ab”}}#CTX#Could not get the
required ExchangeServiceBinding client
(…)
request-id: 1e642da7-5ad4-4c6d-9d58-147ae8999c23
x-ms-diagnostics: 2000001;reason=”The issuer of the token is unknown. Issuer
was ‘00000004-0000-0ff1-ce00-000000000000@212b4cdf-0122-4614-9df5-4c9dd223b61c’
.”;error_category=”invalid_token”
WWW-Authenticate: Bearer client_id=”00000002-0000-0ff1-ce00-000000000000″,
trusted_issuers=”00000004-0000-0ff1-ce00-000000000000@myprimarysipdomain.de”,
error=”invalid_token”,Basic realm=”autodiscover.exchange.server”,Negotiate,NTLM
(i changed myprimarysipdomain.de and autodiscover.exchange.server.)
Do you have any idea?
Greets and thanks for your blog!
I’ve had that cmdlet fail the test on working accounts before so it may not actually be a real problem with the user account.
In short I am struggling with subdomains, because my ad is a subdomain of my dns namespace.
Possible error in your documentation –
I used the following command from the exchange mgmt. shell which was successful and mirrors your screenshot (your text documentation does not)
.\Configure-EnterprisePartnerApplication.ps1 -AuthMetaDataUrl https://fe1./metadata/json/1 -ApplicationType Lync -DomainController DC1
However going to the Skype shell this command fails:
New-CsPartnerApplication -Identity Exchange -ApplicationTrustLevel Full -MetadataUrl “https://autodiscover.jdskype.net/autodiscover/metadata/json/1”
Jeff:
I solved the issue by installing a self signed certificate and installing that certificate in the trusted root folder of the FE server. Great article! -BK
Jeff,
Enter to this phase and few questions arrived…
Is the Exchange URL required? As I entered the setup without the URL and got it work just normally. Autodiscover is based on the DNSes very heavily, but those you should already have in place. So where that URL is needed?
What about if you do have hybrid, what URL you need to use then? Or is that even then needed, as the same principals should work there as well?
You also left the ExchangeAutodiscoverAllowedDomains as empty, was there a reason for that?
Hi Jeff,
Thanks for a very detailed write-up. I have followed all your instructions and successfully created the partnership between my SfB 2015 and Exchange 2016 servers. However, when I issue the “Test-CsExStorageConnectivity” cmdlet, I get an error code 574.
This statement stands out to me: ” Client found response content type of ‘ ‘, but expected ‘text/xml’. ”
Have you run into this problem before?
Never mind. I managed to resolve my issue by resetting the EWS Virtual Directory from the Exchange Control Panel.
You see, the whole time I’d been getting the test failure, I was able to browse manually to the EWS at https://EXCH_FQDN/ews/exchange.asmx from the SKYPE server; it just prompted me for credentials. So I figured there was something wrong with the authentication setup on the EWS and since the test cmdlet didn’t ask for credentials, it was likely failing somehow. I tinkered with various combinations of the authentication settings manually, but none seemed to work. So I finally decided to just reset them to default.
This seems to have cleared out whatever the issue was and I was able to run the test cmdlet successfully.
I got integration working smoothly. The only thing I’m curious about is running Get-CsManagementStoreReplicationStatus displays two Exchange CAS member servers with Replicas that are not up to date. I’m sure Exchange does not require local DB replicas.
Hi Sir
In my scenario, I have MS Exchange 2019 CU1 that has Certificate from Certum Company and its valid in internet but certificate of my Skype for Business 2015 (that has been updated with last CU) is internal Certificate and not vaid in internet.
I mean these servers has different certificate!
Could you please help me how can I integrate them in this scenario?
Best Regards
Could Skype for Business server 2015 integrate with Linux mail server?
No, Microsoft Exchange is required to utilize mailbox and UM features.
Hi Heff,
I have an exchange 2013 farm in one site and an SfB 2015 farm in different site with reverse proxy, edge, front-end and DB roles. I want to know what ports should be opened through firewalls to integrate SfB with Exchange and between which components
uestion on partner apps with Ex2016 and SFB2015.
i have setup the partner app on the skype side using the autodiscover as i should. that has populated to all Front end servers. great.
but i am confused on the exchange side. I have setup the partner app using the FQDN of the front end server in the same datacenter as the Exchange 2016 server.
but i have 3 other locations with a skype FE server.
Do i need to set up them to be a partner app on the exchange 2016 server using the script, as well?
because when i do. and i modify the command to be the fqdn of another FrontEnd server. it comes back and says there is a duplicate entry already with that same info.
i am kind of confused how that works. but logic tells me if the partner app on the exchange server is set with a FQDN of the onsite FrontEnd. that mean the remote offices with a Frontend server, basically pass their requests along to the FrontEnd server with the partner app setup on exchange. which i can see how that just adds an unnecessary hop.
or maybe i am wrong and you only need to run the partnerApp script on exchange to a single Front end?
Hi Jeff, thanks for the great article. Trying to integrate Sfb 2015 with Exchange 2016 and alas, the metadata can’t be found on the front-end, I only get a xml code saying that it’s not found.
is there something to activate before this metadata can be seen ?
NotFoundNonethanks and best regards
Laurent
Hi again Jeff,you can forget my previous question, seems that the oauth certificate was not assigned, after requesting and assigning it, I had access to the medata
thanks and best regards
Hi Jeff,
I hope you’ll be still replying comments on this post. I had previous configured the Exchange 2013- SfB 2015 integration successfully. Recently I was asked to change the published domain name for the setup from domain.net to doman.ir.
I went through changing all URLs, SIP domain and certificate, except for the SfB frond end pool which still remains on the internal AD domain (domain.net).
I am able to browse the Exchange auto discovery URL( https://autodiscover.domain.ir) and the SfB pool URL (https://sfbpool.domain.net/) on each server without any certificate warnings.
I’ve created an enterprise partner application on the Exchange server successfully. But when I try to configure the Exchange server as a new partner application on SfB, it throws an error:
——————————-
Cannot bind parameter ‘MetadataUrl’ to the target. Exception setting “MetadataUrl”: “The metadata document could not be
downloaded from the URL in the MetadataUrl parameter or downloaded data is not a valid metadata document, error: The underlying connection was closed: Could not establish trust relationship for the SSL/TLS secure channel.”
——————————-
Could you please help me resolve this issue.
Regards, Alireza
In the Exchange management shell, entered the command ConfigureEnterprisePartnerApplication.ps1 to configure application partnership with another server ( skype for business) and received the following error message:
Cannot acquire auth metadata document from ‘https://feserver.lync.com/metadata/jason/1’. Error: The underlying connection was closed : Could not establish trust relationship for SSL and TLS Secure Channel
Regards,
Navinkumar S
Kindly help us to resolve the issue
Hey Kumar,
did you check if your server is able to connect to the url? Also check if you get any SSL-Errors when opening the page on a webbrowser. If yes, please ensure the S4B-Server have the correct certificates installed for its web services.
I configured this settings then try test and saw success. But , When I log on Skype client, I received “Exchange needs your credentials.”
Hello Jeff,
Greetings from Texas,
Enjoyed reading your blogs. My question is generic, but I can’t seem to find an easy answer. I was referred to you by a coworker. I just started working on this project and the problem we are seeing is that when we send out Teams meetings, they aren’t auto- accepted. The exchange account we are using is outside our company domain. Any suggestions or ideas would be much appreciated.
Exchange organizations do not auto-accept external meeting invitations by default. That is something that the receiving organization would need to modify (if acceptable/allowed) on the target resource mailbox. https://practical365.com/enabling-external-users-to-book-exchange-room-calendars/
Jeff,
Thank you for the very much for your response, it is very much appreciated. In the link you referred me to, is this something I can edit or implement in Microsoft 365 Admin Center for Teams under Exchange/Mailflow/Rules or does this have to be implemented on the Exchange Server itself for the questionable mailboxes ?
The latter. You need to modify the calendar processing rules on the destination mailbox(es).