This basic article is intended to provide a background in different Active Directory user name and domain name formats and how they are used by applications for basic and integrated authentication process within Windows Server.
The guidance provided throughout is targeted towards working with Microsoft Lync, Exchange, and third-party solutions or applications which support direct registration and authentication to these Microsoft UC platforms.
In most environments registration is as simple as typing in a SIP Address, username, and password which is the same information that native Lync and Outlook clients will leverage for connectivity and authentication. But in some more complex environments it may be necessary to known more specific information about the user accounts used to authenticate clients as these Active Directory deployments can often times use a variety of mismatched user name and domain name formats.
Thus it is beneficial to understand the following concepts in order to identify what is often simply a failure to register due to incorrect entering account credential information. The specifications and limitations of these formats are detailed in this TechNet article.
Domain Names
Active Directory supports two separate types of domain name formats since it’s introduction into Windows Server 2000.
Legacy Domain Name
The Legacy Domain Name parameter, which is also commonly referred to as the NetBIOS Domain Name, is a carryover from Windows NT and is limited to 15-characters. (NetBIOS names are 16-characters in length but the last character is hidden and is used to identify the name record type.) This is the value commonly used with the DOMAIN\username format when signing into various Microsoft applications and even though it is not case-sensitive this string is traditionally shown all in uppercase as a matter of good practice. Although it is considered a legacy format it is still the most prevalently used format today for user authentication.
DNS Domain Name
The DNS Domain Name parameter was added in Active Directory with the release of Windows 2000 and supports up to 24-characters for the hostname portion, but the Fully Qualified Domain Name can be much longer (e.g. subdomain1.subdomain2.domain.com).
As indicated in the screenshots above the sample environment is using a legacy domain name that is shorter than 15 characters so the same string can be used for both formats. This is ideal and is the general best practice used in the field; to select shorter domain names when designing an Active Directory forest so that authentication can be simplified across Microsoft and third-party applications which may use one or both formats. Unfortunately this is not always the case as mergers and divestitures over time can lead to more complicated Active Directory environments. Although newer versions of Windows Server does allow for these domain names to be changed post-deployment this is almost never actually attempted in the field due to the massive impact on the entire environment.
Alternatively the following screenshot shows an AD domain in which the two type use entirely different values (verylongdnsdomainname.com vs. SHORTNAME).
User Names
Just as with domain names there are two different formats in Active Directory for storing user names:
Legacy User Logon Name
The User Logon Name (Pre-Windows 2000) is the legacy format from Windows NT and is often referred to using the raw attribute name of sAMAccountName. This field is limited to a maximum of 20 characters and is used in conjunction with the legacy (or NetBIOS) domain name.
User Logon Name
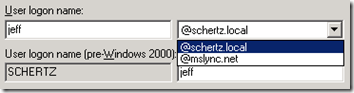
The User Logon Name is a the newer username format which is often mistakenly referred to as the User Principal Name (UPN). That term is used to indicate the entire user name and domain name format.comprised of the User Logon Name and the UPN Suffix which is shown in the drop-down menu in the screenshot below.
Just as with domain name formats the user names can also be unique. Depending on the naming conventions used in the directory it is more common to have long user names truncated to 20 characters in the legacy user name field. In the complex example shown below a user name of 36 characters (e.g. abcdefghijklmnopqrstuvwxyz0123456789) is automatically truncated to only 20 characters in the legacy field.
Authentication Formats
Once the user name and domain name formats are clearly identified then they are assembled into pairs in specific formats to be used for authentication. The ubiquitous NTLM authentication used in Windows Server can support two different formats.
Legacy
The legacy format requires that the Legacy (NetBIOS) Domain Name value is used with the legacy User Logon Name (sAMAccountName).
Simple Example: SCHERTZ\jeff
Complex Example: SHORTNAME\abcdefghijklmnopqrst
User Principal Name
The newer User Principal Name format is comprised of the User Logon Name (not the legacy sAMAccountName) and the UPN Suffix assigned to the specific user account.
Simple Example: jeff@schertz.local
Complex Example: abcdefghijklmnopqrstuvwxyz0123456789@verylongdnsdomainname.com
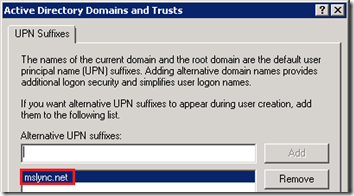
It is important to understand that although the DNS Domain Name is the default assigned UPN Suffix for all user accounts created in the domain this value can be changed and customized in Active Directory. So in the event that the Active Directory namespace (e.g. schertz.local) does not match the Lync SIP Domain namespace (e.g. mslync.net) it is still possible to provide a simplified user sign-in experience by defining an additional UPN suffix which matches the SIP domain and then assigning that suffix to all desired user accounts.
- The following screenshot shows how an additional UPN suffix (e.g. mslync.net) can be added to the forest using the Active Directory Domains and Trusts application.
- Once this is defined then it will appear as a choice for all user accounts in the domain and can be selected in the Active Directory Users and Computer utility.
In the example above it would be possible to provide the same ‘string’ to users as both their SIP Address and User Principal Name even when separate namespaces are used between AD and Lync. This approach allows Lync users to enter the same information for both their Sign-In Address and their User Name. In fact in a recent Cumulative Update for the Lync client the sign-in behavior was changed to actually assume that the AD user name is the same as the SIP address during the first authentication attempt, and then if that fails (due to unique values being used for both) then the User Name field will be presented to the user to fill-out for a second attempt. This change in behavior makes the client more ‘cloud’ friendly as the default configuration for Office 365 and most hosted deployments of Lync will set these fields to the same values.
Hopefully this post has provided some clarity between the different user name formats and in turn help reduce confusion when signing. When the credentials are known to be accurate and in the proper format this make issues much easier to troubleshoot as it takes the uncertainty of out of equation.
![image_thumb[29] image_thumb[29]](http://blog.schertz.name/wp-content/uploads/2012/07/image_thumb29_thumb.png)
![image_thumb[28] image_thumb[28]](http://blog.schertz.name/wp-content/uploads/2012/07/image_thumb28_thumb.png)
![image_thumb[27] image_thumb[27]](http://blog.schertz.name/wp-content/uploads/2012/07/image_thumb27_thumb.png)
![image_thumb[26] image_thumb[26]](http://blog.schertz.name/wp-content/uploads/2012/07/image_thumb26_thumb.png)
![image_thumb[25] image_thumb[25]](http://blog.schertz.name/wp-content/uploads/2012/07/image_thumb25_thumb.png)
![image_thumb[24] image_thumb[24]](http://blog.schertz.name/wp-content/uploads/2012/07/image_thumb24_thumb.png)
Excelent Article! Congratulations!!
that answered my question, thanks for the article!
[…] values are identical, but that is not always the case so do not make any assumptions. This blog article explains Active Directory naming formats in greater […]
Thank you for the good article,
I have a question please, Is it possible to enforce the login to use case sensitive Username? I am using Windows Server 2008 R2 Active Directory.
Thank you,
Islam Thwabeh
No, Usernames are not case-sensitive in Active Directory, only the passwords are.
Greate articale
Thank you!
Hi,I dont want to use user@domain.com as this is creating a problem in my product. Is there any way i can use any other UPN name for my user login
eg…user@sanity.local…..i dont want to use the convention @ i want to user user.sanity.local
???Thanks
Hi Jeff,
I am trying to find an answer to a question for some time already with any luck. I am hopping that you can help me to find the answer for it.
We have created UPN suffix in our active directory in a form of username@company.com and everything works ok except when a user logs into network ( let's say into asp.net app with windows authentication etc) using the UPN login, after logging in the username that is shown is the pre-2000 windows login username. Basically as soon as one uses UPN login usernan to login into network it changes to the pre-2000 windows login name. Do you have any idea why is this happening?
Thanks in advance!
Arman
I’ve not seen that before; can’t say what could be causing it.
Hi
I can see that our organisation uses different UPN suffix for ‘User logon Name’ Attribute in AD than the one in SIP field.
and this tends to bring confusion most of times for external users.
is there a way to simplify this issue?
Regards,
Roy
Roy, the simplest approach is to define an additional UPN suffix in Active Directory that matches the SIP domain in use with Lync and then assign that UPN suffix to all of the AD user accounts. This will ‘hide’ the internal AD namespace from users. Note that this does not address any usage of the legacy NetBIOS domain name as that cannot be changed (without a full domain rename which is never recommended).
Hello Jeff,
How can I use the Identical username for my AD and Exchange 2010 using different UPN Suffix. Need urgent help.
I’m not sure what you are asking here. A single user object can only have one UPN and one username.
Firstly sorry my english, I´m learning yet.
Please, my doubt is, I have one user that the User Logon Name is different of User logon name (pre-Windows 2000).
example: fabio.lacerda in User Logon Name and lacerdaf in User logon name (pre-Windows 2000).
What the principal impact for user ?
Thank you very much!
The only impact is what a user enters to sign-in to Lync. When they (UPN and SIP) are the same then the initial sign-in process is one step less.
Hi Jeff,
I am trying to set up the same as Lacera, I have a customer who has a pre 2000 windows login format of localdomain\ext_sdaly. He wants to log into our OWA with stephen.daly@externamdomain.com.
What I have done is add a UPN suffix for the externaldomain.com, changed the UPN logon method to this, and ensured it matches in exchange.
This is a linked user that authenticates with his AD. It works if I were to login with ext_sdaly@externaldomain.com or ext_sdaly@localdomain.local. But for some reason it won’t work as stephen.daly@externaldomain.com.
Is it because this is a linked user? We have users setup with different UPN logins that are stored in our own active directory but it doesn’t work for this.
Sorry, I don’t know what would be causing that issue. Most likely something in the DNS configuration.
Hi, I know this article is a bit old but I’ve been having an issue with a user who has been having trouble accessing many shares for the past several months despite removing & adding his account to the share and restarting his machine. He has the same issue on other machines as well. His account User Logon Name is different from his pre-windows 2000 logon name.- could this be the reason why he can’t access shared folder?
Possible but I can’t say I’ve seen that. Typically keeping the account names the same resolves a lot of issues so it’s a general best practice to do that.
Hi,
Hoping that you still respond to this great post, but I have seen a format in use that looks like UPN, but is really ‘sAMAccountName@NetBIOS’, for example ‘jeff@SCHERTZ’. You can verify this format, for example, by authenticating to AD using an LDAP tool such as Apache Directory Studio.
Have you come across this format? Are you aware of an official name or reference to it? Is it simply an alias for ‘SCHERTZ\jeff’?
It does appear to be a supported format, refer https://support.microsoft.com/en-us/help/929272/interactive-logon-styles-and-key-distribution-center-account-lookup-in.
this is an old format that I would not include in any best practices discussions. It’s only really applicable in a NetBIOS-only scenario where DNS is not available to properly handle the other formats. I would always use UPN everywhere it’s supported.
For anyone still wondering, it’s commonly used by non-Active Directory products doing Kerberos auth (maybe using a keytab created for a domain account).
The format for a Kerberos “user principal” is generally USERNAME@REALM (REALM = domain name, in AD terms).
If a keytab has been created for a service account in AD using ktpass or other methods for use by a non-AD system, you also may see the UPN in the user account has been formatted like an SPN (i.e. for a “service principal”). So, an account for a web service may have the account UPN configured with a service principal name, like: HTTP/Webserver@example.com. That is the account name it’ll use to authenticate. (I personally prefer to ensure any SPNs are set up correctly in AD using SETSPN as well (which will add entries to the ServicePrincipalName field, not the USERPrincipalName as ktpass does).)
But for a “normal” user logon, USERNAME@REALM is how Kerberos auths the user.
Hi There,
I’m looking for MS documentation of logon name syntax.
Thank you
Regads,
Zoltan
[…] Understanding Active Directory Naming Formats : Jeff … […]
excellent article Jeff. i have a question for you. i have a service that uses the UPN and when restarting the machine it start automatically BUT randomly. when i change from UPN logon style to DOMAIN\user it never fails to start.. what is happening? when using UPN only thing i get is EVENT ID 7000.
thanks!
No clue there, but while UPN is typically the preferred format it appears that whatever service you are using operates better with the legacy format so I’d stick with that then.
Very nice, Thanks alot ,
you have explained it all to gether
regards